Assess and Prioritize Agentic AI Use Cases in Retail
Powered by AI, guided by people.
View Blueprint
Activate Data Governance
Create the rules of engagement for trusted data with a decision-focused framework.
View Blueprint
Align CRM Selection to Your Higher Education Context
Transform CRM selection with self-knowledge and strategic assessment.
View Blueprint
Publish an Annual AI Performance Report
Measure your AI performance to maximize return and mitigate risks with your AI investments.
View Blueprint
Assess and Prioritize Agentic AI Use Cases in Transportation
Focus autonomy where it strengthens reliability, utilization, and service continuity.
View Blueprint
Launch an OT Security Program for Manufacturing
Turn OT security complexity into clear priorities.
View Blueprint
Visualize the Mining Industry of the Future
Envision how digital can propel the transformation of your industry and your organization.
View Blueprint
Configure-Price-Quote Selection Guide
Identify the best tools for your sales automation needs.
View Blueprint
Define Your Business Needs for an Oil and Gas ERP Transition
A guide to gathering and validating the key requirements and considerations for an ERP transformation.
View Blueprint
Build a Data Strategy for Property & Casualty Insurance
Turn fragmented insurance data into reliable, actionable insights.
View Blueprint
Info-Tech’s Best Research for Education 2026
IT leaders are looking to address the uncertainties facing their educational institutions.
View Blueprint
Info-Tech’s Best Research for Manufacturing 2026
IT leaders are looking to address the uncertainties facing their manufacturing operations.
View Blueprint
Info-Tech’s Best Research for Financial Services 2026
IT leaders are looking to address the uncertainties facing their financial services organizations.
View Blueprint
Info-Tech’s Best Research for Professional Services 2026
IT leaders are looking to address the uncertainties facing the professional services environment.
View Blueprint
Info-Tech’s Best Research for Government 2026
IT leaders are looking to address the uncertainties facing Government.
View Blueprint
Adopt a World-Class ITFM Taxonomy
Take the crucial first step in getting your IT financial management house in order.
View Blueprint
Visualize the Higher Education Industry of the Future
Envision how digital can propel the transformation of your industry and your institution.
View Blueprint
Project & Portfolio Management Software Selection Guide
Streamline the process of selecting the right project & portfolio management platform for your organization.
View Blueprint
Identify Use Cases to Inform AI Strategy for Oil and Gas
Choose relevant and feasible initiatives to maximize business impact.
View Blueprint
Build an AI-Driven Supply Chain Resilience Strategy for Retail
Smart AI adoption: Reduce complexity, boost resilience.
View Blueprint
Harness AI to Reduce the Cost and Effort of KTLO in IT Operations
You wanted this yesterday. The tech is here today. Make way for a better tomorrow.
View Blueprint
Select and Prioritize AI Use Cases for Your Law Firm
Balancing value, feasibility, and risk
View Blueprint
Reimagine Business Processes With an AI-First Approach
AI thrives when it follows intentional, optimized workflows.
View Blueprint
Develop a Business-Aligned GIS Strategy for Utilities
Transform GIS into a strategic utility platform.
View Blueprint
Transform Your Transportation Operations With High-Value AI Use Cases
Build an intelligent transportation ecosystem.
View Blueprint
Accelerate AI in Government for Improved Impact and Results
Build foundations first, then accelerate with confidence.
View Blueprint
Board Management Software Selection Guide
Transform boardrooms into engines of strategy, trust, and innovation.
View Blueprint
Build a Technical Reference Architecture for Utilities
Build the utility technology landscape of the future.
View Blueprint
Design a Service Catalog That Drives Insight and Innovation
Cut the complexity and transform your service catalog from a static list into a strategic hub.
View Blueprint
Right-Size Your Enterprise Application Support Team
Stop guessing. Make data-driven decisions about your support team.
View Blueprint
Select a Student Information System for K-12 Education
Clarity at the outset ensures confidence in selection.
View Blueprint
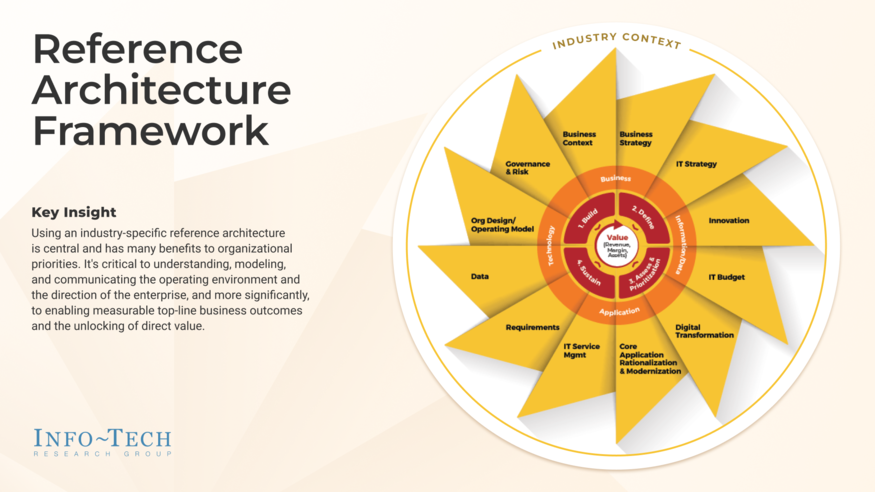
Define Your Industry-Specific Transformation Through Capability Mapping
Turn your reference architecture from insight to impact.
View Blueprint
Build a Resource Plan to Support Integrated IT and Biomedical Device Management
Secure your expanding digital estate.
View Blueprint
Drive Business Value With Microsoft 365 Copilot
Adopt and scale Copilot with intent and trust.
View Blueprint
Modernize Manufacturing Operations Using High-Impact AI Use Cases
Translate AI ambition into measurable outcomes.
View Blueprint
Visualize Your Strategic Roadmap With Power BI
Create visibility to shape the strategy.
View Blueprint
Rebuild Your Talent Engine: Attract and Retain IT Talent in Insurance
A practical strategy guide for insurers to strengthen talent outcomes in the face of modernization and workforce attrition.
View Blueprint
Build a Next-Gen Retail Tech Stack Roadmap
Power smart retail with AI, from warehouse to checkout.
View Blueprint
Build a Sustainable Knowledge Transfer Strategy
Transfer IT knowledge before it’s gone.
View Blueprint
Prioritize and Implement Construction Robotics to Support Your Workforce
Redefine the future jobsite.
View Blueprint
Build an Integrated Enterprise Risk Management Program
A holistic framework to manage enterprise risk in today’s complex and unpredictable environment.
View Blueprint
Establish Your Adaptive AI Governance Program: From Principles to Practice
Prepare your organization for agentic AI and tomorrow’s AI technologies and solutions.
View Blueprint
Build a Construction IT Resourcing Plan in Hospitality
Secure IT resourcing needs to drive construction project success.
View Blueprint
Develop a Plan to Overcome Your Microsoft Power Apps Challenges
Address key challenges before adopting a wide-scale transformation.
View Blueprint
Build a Digital Health Strategy for Your Healthcare Organization
Align business and IT priorities to drive connected, resilient, and data-driven care.
View Blueprint
Launch Products Faster With Modern Product Lifecycle Management Systems
Accelerate your design to delivery processes by integrating engineering, operations, and IT.
View Blueprint
Assess Readiness and Value for Policy-as-Code
Chart the right path toward value realization with automated policy management.
View Blueprint
Build Your Applications Practice Strategy
Delivering value starts with embracing what your practice should be.
View Blueprint
Legal Industry Business Reference Architecture
Positioning your firm to compete effectively in tomorrow’s legal market.
View Blueprint
Build a Business-Aligned IT Strategy
Success depends on IT initiatives clearly aligned to business goals, IT excellence, and driving technology innovation.
View Blueprint
Master Certificate Lifecycle Management
Enable crypto-agility for the security, scalability, and automation to empower your organization’s digital trust.
View Blueprint
Extend Enterprise Architecture to Operational Technology for Utilities
From strategy to grid: A practical walkthrough of EA for AMI.
View Blueprint
Scale Remote Patient Monitoring to Improve Healthcare Services
Shifting RPM from projects to organizational strategy.
View Blueprint
Retail Business Reference Architecture
Enable agility, scalability, and transformation.
View Blueprint
Contract Lifecycle Management Platform Selection Guide
Fast-track your CLM selection journey and build a future-ready contracting function.
View Blueprint
The Security Playbook
8 Secrets & 12 Steps to Systematically Achieve Security Excellence
View Blueprint
Align Your P&C PAS With the Right Modernization Pathway
Align your PAS choice with the right modernization pathway to maximize agility, compliance, and customer value.
View Blueprint
Identify Use Cases to Inform an AI Strategy for Professional Services
From promise to practice: Select and prioritize AI use cases for professional service organizations.
View Blueprint
The Infrastructure and Operations Playbook
8 Secrets & 12 Steps to Systematically Achieve I&O Excellence
View Blueprint
Identify and Select AI Use Cases to Pilot in the Education Sector
Go from idea to impact with a value-driven selection process.
View Blueprint
Build a Public Sector Shared Services Organization
A five-phase roadmap to improve service quality, reduce duplication, and modernize public sector operations.
View Blueprint
The Applications Playbook
8 Secrets & 12 Steps to Systematically Achieve Application Excellence
View Blueprint
GRC Software Selection Guide
Outdated GRC tools create risk – selecting the right integrated GRC tool is how you stop it.
View Blueprint
Leverage Risk to Inform IT Outsourcing Requirements
Set yourself up to create an outcome-oriented RFP.
View Blueprint
Infrastructure and Operations Priorities 2026
Infrastructure meets IT’s moment.
View Blueprint
Data Priorities 2026
AI and automation amplify whatever data they consume. Feed them noise, and they’ll scale confusion. Feed them clarity, and they’ll scale intelligence.
View Blueprint
Define Transportation Data & Analytics Opportunities to Accelerate Transformation
Unify data for smarter, faster, resilient logistics.
View Blueprint
Cut Costs by Leveraging AI Solutions
AI uncovers savings that traditional methods can’t reach.
View Blueprint
Defend Against Deepfake Cyberattacks
Use a cyberthreat assessment approach to determine your organization’s exposure to deepfake attacks.
View Blueprint
Leverage AI for Information Management
From complexity to clarity: AI-powered information management.
View Blueprint
Design the IT Infrastructure & Operations Organization of the Future
Review your strategy, structure, skills, and staffing.
View Blueprint
Empower Your Business With a Proven Cloud Strategy
Make confident cloud decisions with a strategy grounded in patterns, principles, and purpose.
View Blueprint
Identify and Respond to Credible Threats Arising From Global Uncertainty
Proactively manage the impact of macro uncertainties on your organization.
View Blueprint
Future-Proof Your Warehouse Operations With Modern Warehouse Management Systems
Use technology to unlock the potential of your warehouses.
View Blueprint
Invest in Realistic and Comprehensive Project Costing
Do the math now so that you can defend the spend later.
View Blueprint
Modernize Your Data Strategy to Enable AI/ML in Banking
Your bank is rushing to adopt AI/ML; modernizing your data strategy is critical for success.
View Blueprint
The Future of the Oil and Gas Industry
Industry trends shaping future business opportunities.
View Blueprint
Fast-Track Your Enterprise Service Design
Design a sustainable enterprise service customers want to use, employees want to support, and the organization wants to finance.
View Blueprint
Build an Enterprise Application Integration Strategy
Transform from chaotic disintegration to seamless integration.
View Blueprint
Strengthen Your Organization’s Digital Sovereignty
Move sovereignty forward with practical action.
View Blueprint
Develop a Strategic Plan for Intelligent Application Security
Plan for an intelligent SSDLC to build smarter, faster, and more resilient solutions.
View Blueprint
Deliver Digital Products at Scale
Deliver value at the scale of your organization through defining enterprise product families.
View Blueprint
Define Hospitality Data Requirements to Accelerate Transformation
Align data and amplify value to reimagine hospitality.
View Blueprint
Build Learning Agility in Your IT Team
Agility isn’t a course you take; make it an everyday practice in IT.
View Blueprint
Construct With Confidence Using the Right Construction Management System
Narrow your CMS search and align your tools to your needs.
View Blueprint
Accelerate Strategic Resource Planning for Core System Replacement in US State Government
A structured approach to building a strategic resource plan aligned with the critical needs of legacy modernization and core system replacement in government
View Blueprint
Integrate IT/OT Business Continuity Planning and Disaster Recovery
Minimize disruptions by breaking down IT/OT silos.
View Blueprint
Modernize Your Loyalty Program Through a Digital Strategy
Find your place in the digital economy.
View Blueprint
Modernize Healthcare Systems: A Buyers Guide to Electronic Health Records
Select the right EHR to align clinical priorities, reduce technical debt, and deliver sustainable operational improvements.
View Blueprint
Build a Data Strategy for Professional Service Organizations
A pragmatic roadmap for B2B firms to drive client-centric outcomes.
View Blueprint
The Future of the Transportation & Logistics Industry
Industry trends shaping future business opportunities.
View Blueprint
Implement Whole-of-Government Information Security Governance
Rethinking how governments provide cybersecurity services at all levels, moving toward a "whole-of-government" integrated model.
View Blueprint
Adapt to Uncertainty With a Technology-First Action Plan for Nonprofits
Cost cutting in times of crisis works; doubling down on innovation works even better.
View Blueprint
AI Customer Experience Tools: Buyers Guide and Market Trends
Utilizing AI in customer experience will improve customer service.
View Blueprint
Business Reference Architecture for US State Governments
Drive innovation solutions by accelerating the building of your agency’s organizational business capability map, defining strategic focus, and prioritizing key capabilities and capability gaps.
View Blueprint
Improve Your API Processes to Secure Your Fintech Integrations
Implementing and configuring your API gateway is critical to securing your fintech integrations.
View Blueprint
The Enterprise Architecture Playbook
12 Steps to Systematically Achieve Enterprise Architecture Excellence
View Blueprint
Digital Experience Platform Selection Guide
Speed up the process to build your business case and select your DXP solution.
View Blueprint
Empower Not-For-Profits With AI and ML
Explore AI use cases to transform your not-for-profit.
View Blueprint
Assess Your Data Science and Machine Learning Capabilities
Unlock the full potential of AI and data.
View Blueprint
Build Your EA Practice Strategy
Craft the practice your organization needs to solve the problems your stakeholders care about the most.
View Blueprint
Build a Security Compliance Program Aligned to NPSNet Policy With ITSG-33
Bridge the gap between policy and practice while accelerating NCACR readiness.
View Blueprint
Transform Table Operations With SmartPit Technology
Effortless play, seamless management, and ultimate efficiency
View Blueprint
Equip Your Business for the Future With the Right Transportation Management System
Narrow your TMS search and find a solution that fits your needs.
View Blueprint
Visualize the Manufacturing Industry of the Future
Envision how digital can propel the transformation of your industry and your organization.
View Blueprint
Visualize the Industry of the Future
Envision how digital can propel the transformation of your industry and your organization.
View Blueprint
Standardize the Service Desk
Build a solid foundation for future IT service improvements.
View Blueprint
Establish the Target Operating Model Needed to Execute Your Data Strategy
Engineer a data management model that is co-owned, co-designed, and strategically aligned.
View Blueprint
Navigate IT Priorities Through Leadership Shifts
Strategies for Canadian government CIOs to ensure stability, agility, and innovation.
View Blueprint
Mitigate ERP Cloud Migration Risks for Utilities
Anticipate disruption, strengthen controls, and sustain operational integrity.
View Blueprint
Transition and Operationalize Incoming Projects
Create a document and release process that prepares the operational and support team to take over project support on launch day.
View Blueprint
Build Your AI Strategy and Roadmap
Develop your AI strategy to maximize return and mitigate risks with your AI investments.
View Blueprint
Modernize Your Manufacturing Operations Using Connected Technologies
Take the right actions to advance the smart factory agenda.
View Blueprint
Adapt to Uncertainty With a Technology-First Action Plan for Healthcare
Cost cutting in times of crisis works; doubling down on innovation works even better.
View Blueprint
Assess the Maturity of Research Computing in Higher Education
Assess, prioritize, and elevate IT services to drive institutional excellence.
View Blueprint
Take Control of IT’s Narrative
Transform IT’s brand by redefining outdated and faulty perceptions.
View Blueprint
Navigating the ERP Landscape for the Construction Industry
Narrow your ERP search, find a fit-for-purpose solution.
View Blueprint
Launch Your Hospitality Innovation Initiative to Success
Value-driven innovation, beyond technology.
View Blueprint
Implement an AI-Orchestrated Service Desk
Build a strategic approach to drive automation and efficiency.
View Blueprint
Adapt to Uncertainty With a Technology-First Action Plan for Government
Create a plan for thriving – not just surviving.
View Blueprint
Build and Select AI Use Cases for Health Insurance
Prioritize AI use cases to transform your organization.
View Blueprint
Info-Tech’s Best of 2025 Mid-Year Report: IT Moves From Disruption to Decisive Action
IT leaders are embracing change – and moving into readiness mode across domains.
View Blueprint
Professional Services Business Reference Architecture
Your guide to building business capability maps, value streams, and strategy maps in the professional services industry.
View Blueprint
Elevate IT Satisfaction by Strengthening Stakeholder Relationships
Technology is easy, people are hard. Stop dismissing stakeholder relations as a charming “soft skill” and instead recognize it as a critical driver for achieving business objectives.
View Blueprint
Adapt to Uncertainty With a Technology-First Action Plan for Higher Education
Cost cutting in times of crisis works; doubling down on innovation works even better.
View Blueprint
Adapt to Uncertainty With a Technology-First Action Plan for Retail
Cost cutting in times of crisis works; doubling down on innovation works even better.
View Blueprint
Build and Select AI Use Cases for Wealth and Asset Management
Prioritize AI use cases to transform your firm.
View Blueprint
Implement AI for Customer Experience
Use AI to supercharge your customer experience outcomes and propel your brand forward
View Blueprint
Adapt to Uncertainty With a Technology-First Action Plan for Manufacturing
Respond faster, operate smarter, and adapt continuously in the face of constant change.
View Blueprint
Launch a Customer-Centric Data-as-a-Product Journey
Leverage data as a strategic asset to unlock its full potential.
View Blueprint
Define the Components of Your AI Architecture
Set up the foundation of your AI architecture for success.
View Blueprint
The Future of Non-Durable Goods Manufacturing
Trends shaping future business opportunities
View Blueprint
Establish an Integrated IT-Business Operating Model
Strategically embed technology capabilities across the enterprise to engage and enable the organization.
View Blueprint
Adapt to Uncertainty: Optimize Your Top Areas of IT Spend
Info-Tech LIVE 2025: Keynote Presentation
View Blueprint
Sync or Sink: Aligning IT and HR for the Future of Work
Info-Tech LIVE 2025: Keynote Presentation
View Blueprint
Building the Road to Governing Digital Intelligence
Info-Tech LIVE 2025: Keynote Presentation
View Blueprint
An Operational Framework for Rolling Out AI
Info-Tech LIVE 2025: Keynote Presentation
View Blueprint
Fueling AI Greatness: The Critical Role of Data & AI Literacy
Info-Tech LIVE 2025: Keynote Presentation
View Blueprint
Leading People Change in the Face of Disruptive Technology
Info-Tech LIVE 2025: Keynote Presentation
View Blueprint
Digital Transformation: A Revolution That Lost Its Way
Info-Tech LIVE 2025: Keynote Presentation
View Blueprint
Comparing Software Practices in Maturing IT
Info-Tech LIVE 2025: Keynote Presentation
View Blueprint
Enterprise Application Change: It's All About Business Capabilities
Info-Tech LIVE 2025: Keynote Presentation
View Blueprint
The Evolution of Professional Services
Trends shaping the future of professional services organizations
View Blueprint
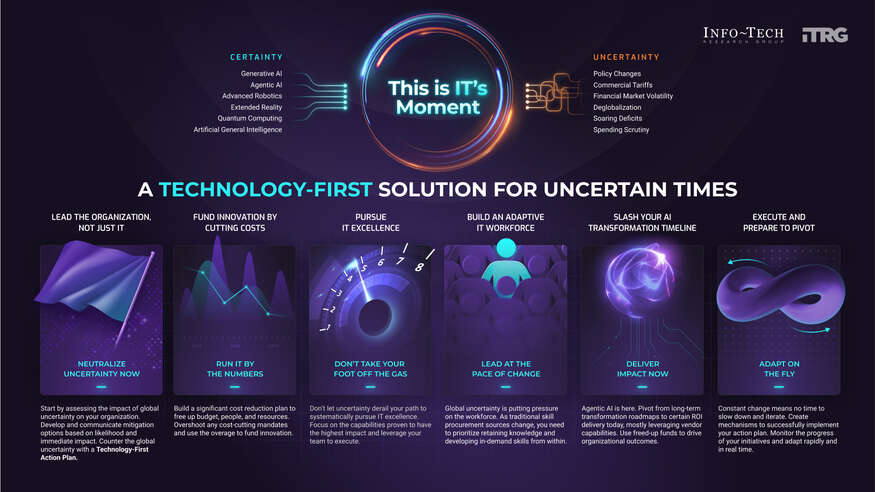
Adapt to Uncertainty With a Technology-First Action Plan
Cost cutting in times of crisis works; doubling down on innovation works even better.
View Blueprint
Build Your IT Cost Optimization Roadmap for Higher Education
Improve cost-to-value in a sustainable manner.
View Blueprint
Achieve CMMC Compliance Effectively
Take a structured approach to Cybersecurity Maturity Model Certification.
View Blueprint
The Essential IT Playbook
12 Steps to Excellence in Managing IT in Small and Midsize Enterprises
View Blueprint
Understand and Assess IT Skills Gaps for Industry 4.0 & 5.0
Implement a strategic approach to skills development and acquisition to capitalize on the benefits of Industry 4.0 & 5.0.
View Blueprint
Build a Robust Security Architecture With Microsoft Technologies
Maximize your investment in Microsoft security tools and justify where supplements are required.
View Blueprint
Build a Vendor Security Assessment Service
Use a risk-based approach to right-size your vendor security assessments.
View Blueprint
Build & Execute an Enterprise Device Management Strategy
Build a digital workplace for the workforce of the future.
View Blueprint
Build Your AI Risk Management Roadmap
Develop your AI risk management framework to mitigate risk and drive value for your AI investments.
View Blueprint
Build Seamless IT Operations With Automation
Create a framework to improve processes, reduce risks, and scale effectively.
View Blueprint
Build Your AI Strategy for Retail Inventory Management
Identify value-driven AI strategy use cases to transform your inventory management.
View Blueprint
Keep Transportation Operations Moving in a Shifting Market
Tackle tariffs and demand swings with smart risk planning.
View Blueprint
Build Resilience: Strengthening Construction Amid Policy Shifts
Stay ahead of tariffs and disruptions with proactive risk planning.
View Blueprint
Hold the Line to Drive Government IT Forward
How public sector CIOs can lead through turbulence.
View Blueprint
Develop an M&A IT Playbook
Structured for certainty, adaptable to nuance: the playbook proactively drives M&A success, from due diligence to integration.
View Blueprint
Get Started With AI Red-Teaming
Develop your AI red-teaming practices to effectively mitigate AI and security risks.
View Blueprint
Goods Transportation & Logistics Industry Business Reference Architecture
Your guide to building business capability maps, value streams, and strategy maps for the goods transportation & logistics industry.
View Blueprint
Determine When You Should Use Synthetic Data
Clarify the value that synthetic data can offer your organization and data program.
View Blueprint
Reference Architecture for Oil & Gas
Capability Maps, Value Streams, and Strategy Maps for Oil & Gas Companies
View Blueprint
Build Your Data Strategy to Improve Your Product Mix
Identify value-driven data strategy use cases to transform your product mix.
View Blueprint
Transform Your Professional Services Organization With a Tech-Enabled Digital Business Strategy
A digital business strategy exemplar for legal services.
View Blueprint
Define Your Cloud Vision for the Insurance Industry
A strategic approach to migrate to cloud.
View Blueprint
Assess the Strategic Context for ERP Modernization in Higher Education
High costs and high rewards for institutional IT.
View Blueprint
Fight Financial Crime With Effective Customer Identity and Access Management
Use advanced capabilities to assure identity and prevent financial crime.
View Blueprint
The Future of the Construction Industry
Industry trends shaping future business opportunities
View Blueprint
Build a Strategy to Modernize Your Infrastructure
Align your business and IT goals, then define your guiding principles to set direction.
View Blueprint
Boost Solution Delivery Throughput With AI
Embed AI into the DNA of your solution delivery team.
View Blueprint
Create a Zero Trust Implementation Plan
Build a path to seamless security and verified trust.
View Blueprint
Build a Robust and Comprehensive Data Strategy
Build a data strategy that’s organization first, not technology first.
View Blueprint
Improve Organizational Resilience With a Tabletop Program
Don’t just plan for resilience – practice it.
View Blueprint
Build an ITFM Improvement Roadmap
Find the ideal entry point for maturing your practice of IT financial management.
View Blueprint
Integrate Sustainability Into Your Technology Strategy
The time to act is now: Advance your utility sustainability journey through technology leadership and practices.
View Blueprint
Develop an AI Compliance Strategy
Provide actionable steps for your teams to align with global AI standards.
View Blueprint
Rapidly Improve Your IT Processes
Invest time in process improvement today to save time tomorrow.
View Blueprint
Revolutionizing Retail With Smart Pricing and Promotion
Unlock your full growth potential.
View Blueprint
Lessons Learned and Life After a Breach in Your Healthcare Organization
Mitigate third-party ransomware risks beyond IT disaster recovery plans.
View Blueprint
Drive Vision Alignment for Successful Construction Projects in Hospitality, Gaming & Entertainment
Build aligned and future-ready renovations and new builds.
View Blueprint
Accelerate Your Smart Factory Initiatives Using a Next-Generation MES
Don’t let a legacy manufacturing execution system (MES) hold you back.
View Blueprint
Optimize Jail Management Systems: Navigating the Vendor Landscape for Future-Ready Compliance
Empowering justice systems with compliant, secure, and scalable solutions.
View Blueprint
Ensure Business Alignment in Managed Service Agreements
Prepare your organization to maximize value from your managed service providers.
View Blueprint
Navigating Leadership Transitions in Government
Potential policy shifts and a CIO’s roadmap for the next administration.
View Blueprint
Applications Priorities 2025
Face off against applications disruptors in the coming year.
View Blueprint
Security Priorities 2025
Safeguard your organization by preparing for growing cybersecurity challenges.
View Blueprint
Infrastructure & Operations Priorities 2025
Shift I&O into strategic gear to showcase its true value.
View Blueprint
Construction Industry Reference Architecture
Your guide to building business capability maps, value streams, and strategy maps in both vertical and horizontal construction industries.
View Blueprint
Info-Tech’s Best of 2024 Report: IT Moves Into Position
IT gets the playbook to future-proof the organization.
View Blueprint
Create a Service Management and IT Operations Strategy
Move from assessment to action, using an interconnected approach to meet organizational goals.
View Blueprint
Improve Your PPM Maturity Holistically Across IT/OT
Become more effective in realizing change while removing organizational silos as IT/OT convergence occurs.
View Blueprint
K-12 Education Industry Reference Architecture
Capability maps, value streams, and strategy maps for K-12 education.
View Blueprint
Safeguard Your Data When Deploying AI in Your Insurance Systems
Protect PII by leveraging AI to reduce your risk of exposure.
View Blueprint
IT Talent Trends 2025
Moving beyond the traditional building blocks to focus on the talent trends that will matter in 2025.
View Blueprint
Ground Your Institution for Higher Education’s Future Shock
2024 Institutional IT Benchmark Report
View Blueprint
Revolutionize Ticketing Systems: Enhancing Security, Speed, and Fan Experience With Next-Gen Solutions
Ticketing solutions that create a strategic shift across the technological ecosystem.
View Blueprint
Explore Next-Generation Core Banking Vendors to Unlock New Capabilities and Outpace Competition
Understand the value of next-generation cores beyond the traditional players.
View Blueprint
Build Your Enterprise Innovation Program
Transform your business by adopting the culture and practices that drive innovation.
View Blueprint
Leverage a Rapid Application Selection Framework to Support Youth and Family Services Agencies
A best-practices roadmap for child welfare practices and service delivery.
View Blueprint
Evaluate Congestion Charging Technologies for Innovative Traffic Management
Transform traffic management with technology.
View Blueprint
Launch Cyber Insurance Support Services
Leverage technology service capabilities to meet cyber insurance needs.
View Blueprint
Wireframe Your Generative AI Solution Design
Use Info-Tech's design methodology to align technical solutions with organizational needs.
View Blueprint
Stop Wasting Time Evaluating Commoditized Products and Services
Exponential IT will drive all organizations toward simplified procurement processes for commodity products and services.
View Blueprint
Assess Telehealth and Patient Self-Management Readiness
The crucial role of patient engagement in population health management.
View Blueprint
Leverage Artificial Intelligence to Overcome Resource Constraints and Technical Debt
Empower your digital transformation through intelligent automation and innovation.
View Blueprint
Build a Holistic Data Strategy for Your Healthcare Organization
Develop a data strategy to become a data-driven organization and maximize the value of data.
View Blueprint
Deliver Engaging Portfolio Reports With Power BI
Help executive decision-makers lead from a position of knowledge.
View Blueprint
Develop a Comprehensive IAM Improvement Strategy
A successful identity and access management program is built on solid foundational processes.
View Blueprint
Select the Right Insurance Policy Administration System for Life and Annuity
Determine the value an effective PAS can bring to the business.
View Blueprint
Optimize Enrollment Management for K-12 Education
Understand the value an effective enrollment management system can bring to schools and districts.
View Blueprint
Build a Market-Ready iGaming Strategy
Don’t leave your online casino strategy up to chance.
View Blueprint
Redefine Enterprise Architecture for Smart Manufacturing
Build the right strategy to adopt smart technologies in manufacturing.
View Blueprint
IT Spend and Staffing Benchmarking: Realign Resources for Success
Info-Tech LIVE 2024: Keynote Presentation
View Blueprint
Bending the Exponential IT Curve Keynote
Transform IT so it can be in a position to deliver value-driving, transformative business capabilities.
View Blueprint
The CIO Playbook: 8 Secrets and 12 Steps to Systematically Achieve IT Excellence
Info-Tech LIVE 2024 Keynote Presentation
View Blueprint
Leverage Metrics and Benchmarks to Evaluate LLMs
Navigate the LLM marketplace to find models that meet your needs, minimize costs, and maximize performance.
View Blueprint
Strengthening the CIO Brand: From Perception to Reality
Info-Tech LIVE 2024: Keynote Presentation
View Blueprint
IT Management & Governance: The Next Evolution
Info-Tech LIVE 2024: Keynote Presentation
View Blueprint
Crack the Code to Successful Transformation Management
Info-Tech LIVE 2025: Keynote Presentation
View Blueprint
Explore Healthcare Enterprise Large Language Model Solutions
A buyers guide for ambient AI scribe and revenue cycle management solutions.
View Blueprint
Understand Modern Cybersecurity Solutions for Manufacturing IT & OT
Use intelligent defense software and continuous monitoring to maintain operational integrity.
View Blueprint
Drive a Fit-for-Purpose IT/OT Convergence Improvement Plan for Your Utility
Assess the state of your IT/OT convergence maturity and get ready for the inevitable end state.
View Blueprint
Unlock Value-Driven IoT Use Cases to Transform Your Retail Operations
Implement IoT in retail.
View Blueprint
Secure Your Perimeterless Network
Build an effective tooling strategy based on zero trust security principles.
View Blueprint
Explore AI and AI-Related Use Cases for Credit Unions and Small Banks
Unlock value-driven AI use cases to transform your organization.
View Blueprint
Explore the Art of the Possible for Exponential IT
As technology moves exponentially, so must your entire organization – led by IT.
View Blueprint
Drive Adoption and Sustain Transformational Change
Champion OCM and leave nothing behind.
View Blueprint
Prioritize AI Use Cases for Education
Address the potential of AI to transform education.
View Blueprint
Get Ready to Deliver AI Services
Leverage your existing capabilities to deliver competitive offerings in the new AI services Industry.
View Blueprint
Modernize Your Identity Authentication Practices
Securely manage your identities and improve your authentication based on risks.
View Blueprint
Build an Autonomous Security Delivery Roadmap
Let AI drive real-time risk decisions to combat the exponentially increasing cyberthreat.
View Blueprint
Establish a Vendor Management Roadmap to Succeed With Autonomous Technologies
Mature your vendor management initiative (VMI) to get the most from your vendors and next-generation technologies.
View Blueprint
Revitalize Fan Engagement for Events and Premium Suite Sales
Leverage proven success strategies from adjacent industries for the sports & entertainment industry.
View Blueprint
Elevate Your Service Capabilities to Drive Enterprise Value
Build a roadmap to shift from IT-centric to enterprise service management practices and drive toward an Exponential IT future.
View Blueprint
Core Systems Replacement in Government
Adopting a holistic approach and a strategic shift-left mindset
View Blueprint
Prepare for AI Regulation
Understand current AI legislative initiatives and prepare your organization for future AI regulations.
View Blueprint
Navigate the HIPAA Landscape
Understanding policies and best practices for privacy and security compliance in alignment with evolving regulations.
View Blueprint
Establish a Roadmap for Integrated and Dynamic Risk Management
Up your risk management game to tackle exponential technology risks.
View Blueprint
Define a Data Practice Strategy to Power an Autonomous Enterprise
Deliver the processes, capabilities, and technologies to service AI’s demand for data
View Blueprint
Build Your Exponential IT Product Practice
Build an actionable product practice roadmap that drives enterprise results.
View Blueprint
Transform PPM to Optimize Value From Every Investment
Develop a game plan for integrating AI into your PPM practices.
View Blueprint
Build a FinOps Strategy to Enable Dynamic Cloud Cost Management
Maximize cloud value to power exponential technologies.
View Blueprint
Build a Reporting and Analytical Insights Strategy
Deliver actionable business insights by creating a business-aligned reporting and analytics strategy.
View Blueprint
Consider Agile for Banking
Understanding the core elements of Agile and its suitability with other methodologies in banking.
View Blueprint
Implement an Adaptive System for IT Financial Management
Pave the way for exponential technologies with agile financial practices
View Blueprint
Priorities for Adopting an Exponential IT Mindset in the Non-Durable Goods Manufacturing Industry
Adopting Exponential IT is critical for business growth and sustainability.
View Blueprint
Priorities for Adopting an Exponential IT Mindset in the Technology Service Provider Industry
Adopting Exponential IT is critical for business growth and sustainability.
View Blueprint
Priorities for Adopting an Exponential IT Mindset in the Chemical & Pharmaceutical Manufacturing Industry
Adopting Exponential IT is critical for business growth and sustainability.
View Blueprint
Priorities for Adopting an Exponential IT Mindset in the Retail Industry
Adopting Exponential IT is critical for business growth and sustainability.
View Blueprint
Priorities for Adopting an Exponential IT Mindset in the Food & Beverage Manufacturing Industry
Adopting Exponential IT is critical for business growth and sustainability.
View Blueprint
Priorities for Adopting an Exponential IT Mindset in the Wholesale Industry
Adopting Exponential IT is critical for business growth and sustainability.
View Blueprint
AI in Retail & Wholesale Loss Prevention
Using game-changing technology to transform loss into leadership.
View Blueprint
Priorities for Adopting an Exponential IT Mindset in Local Government
Adopting Exponential IT is critical for driving innovation, efficiency, and value for citizens.
View Blueprint
Priorities for Adopting an Exponential IT Mindset in the Durable Goods Manufacturing Industry
Adopting Exponential IT is critical for business growth and sustainability.
View Blueprint
Build a Software Quality Assurance Program
Build a robust strategy and ensure quality is at the core of everything you do.
View Blueprint
Priorities for Adopting an Exponential IT Mindset in the Utilities Industry
Adopting Exponential IT is critical for resilience and adaptability.
View Blueprint
Build Your AI Solution Selection Criteria
Get to the right questions with a look through the buyer’s lens.
View Blueprint
Transform Manufacturing by Mitigating the Challenges of Industry 4.0 and 5.0
Overcome stagnation by decoding the complexities of Industry 4.0 and 5.0.
View Blueprint
Priorities for Adopting an Exponential IT Mindset in K-12 Education
Adopting Exponential IT is critical for relevance and resiliency in today’s environment.
View Blueprint
Priorities for Adopting an Exponential IT Mindset in the Gaming & Hospitality Industry
Adopting Exponential IT is critical for business growth and sustainability.
View Blueprint
Priorities for Adopting an Exponential IT Mindset in the Sports & Entertainment Industry
Adopting Exponential IT is critical for business growth and sustainability.
View Blueprint
Priorities for Adopting an Exponential IT Mindset in Federal Governments
Adopting Exponential IT is critical for driving innovation, efficiency, and value for citizens.
View Blueprint
(Re)Calibrate Your IT Workforce for AI
Align your workforce with the evolving landscape of AI technology.
View Blueprint
Priorities for Adopting an Exponential IT Mindset in Higher Education
Adopting Exponential IT is critical for relevance and resiliency in today’s environment.
View Blueprint
Analyze Your ITSM Ticket Data
Take a data-driven approach to service desk optimization.
View Blueprint
Build a Water Utility Digital Twin Roadmap
A tactical plan for enhancing your capability development.
View Blueprint
Unify IT in the Education Sector
The intersection of local insight and organizational excellence.
View Blueprint
Bring Your Factory to Life With Smart Manufacturing 5.0
Using human-technology synergy to drive exponential growth and productivity.
View Blueprint
Harmonizing Complexity: Control Tower Integration
Providing manufacturers with real-time integrated supply chain views for quick decision-making.
View Blueprint
Create an Exponential Impact on Hospitality With Service Robots
Revolutionize hospitality through robotics.
View Blueprint
COPS Business Reference Architecture
Business capability maps, value streams, and strategy maps for community-oriented policing services (COPS).
View Blueprint
Overcome the Barriers to Enable Exclusive Premium Experiences
Info-Tech Research Group & Association of Luxury Suite Directors (ALSD) 2023 Survey
View Blueprint
Responsible Use of AI in Policing
Key initiatives to ensure the responsible and ethical use of AI in policing.
View Blueprint
AI and AI-Related Use Case Library for Community-Oriented Policing Services
Unlock value-driven AI use cases to transform your organization.
View Blueprint
Fast-Track Your DERMS Business Case
Speed up the process to justify the need for a distributed energy resources management system (DERMS) solution.
View Blueprint
Integrate Biomedical Device Management With IT
A programmatic approach to enhancing security, efficiency, and collaboration.
View Blueprint
Prepare to Negotiate Your Generative AI Vendor Contract
Build risk awareness: You can’t begin to negotiate until you understand where your real risk points are.
View Blueprint
Deploy AIOps to Improve IT Operations
Transform your organization and revolutionize IT Operations by fostering a data-driven approach.
View Blueprint
Develop an Exponential IT Roadmap
Evolve IT to harness unprecedented opportunities in the era of exponential technologies.
View Blueprint
Use ChatGPT Wisely to Improve Productivity
The AI will mostly beat you to an answer. But is it valid? Ask better questions.
View Blueprint
Interoperability: The True Power Behind the Digital Front Door
What the Fast Healthcare Interoperability Resources mandate means for global digital health trends, and eight key insights into unlocking the full potential of the digital front door.
View Blueprint
Digital Use Case Library for Oil & Gas
Identify the potential digital use cases to transform your organization.
View Blueprint
AI-Powered Precision Medicine to Improve Patient Outcomes
A framework to validate the accuracy, safety, and effectiveness of AI in patient care.
View Blueprint
Responsible AI Primer and Playbook for Public Health and Healthcare Organizations
Leverage the power of AI to improve individual and population health outcomes.
View Blueprint
Promote Data Literacy in Your Organization
Accelerate the uplift of data literacy by breaking down data management concepts into personas with defined learning objectives.
View Blueprint
Define Your Enterprise IT and Digital Services
Grow beyond the IT department that builds solutions and become the business partner that delivers value.
View Blueprint
Real-Time Transportation Visibility (Logistic Visibility Systems)
Whenever and wherever your supply chain is traveling, real-time visibility is the telescopic tower you can use to view its current state.
View Blueprint
Supply Chain as a Service
How will supply chain as a service remodel the retail and wholesale industry?
View Blueprint
AI for Good: A Framework to Support Vulnerable People in Society
The potential for AI to help those who need it the most.
View Blueprint
Simplify Your Journey to Become a Digital Government by Building Cloud Proficiency
Leverage lessons learned in the form of a cloud proficiency assessment.
View Blueprint
Build an Information Security Strategy for Small Enterprises
Small enterprises need a security strategy just like any other sized enterprise.
View Blueprint
Pharmaceutical Manufacturing Industry Reference Architecture
Business capability maps, value streams, and strategy maps for the Pharmaceutical Industry.
View Blueprint
Food & Beverage Manufacturing Industry Reference Architecture
Business capability maps, value streams, and strategy maps for the Food & Beverage Industry.
View Blueprint
Chemical Manufacturing Industry Reference Architecture
Business capability maps, value streams, and strategy maps for the Chemical Industry.
View Blueprint
AI Impact on Customer-Facing Value Chains in Banks
Reshaping old business capabilities into new AI-powered value chains.
View Blueprint
Automation to Reduce the IT Talent Gap in Public Sector IT
Bridging the IT talent gap with smart automation.
View Blueprint
Build an Information Security Strategy
Align the information security strategy to organizational goals and risks to create value.
View Blueprint
Assess the Value Drivers Within Your Solutions
Implement a balanced value measurement framework to align product roadmaps and projects with enterprise goals.
View Blueprint
Autonomous Technologies in Manufacturing
Elevate your operations through the transformative power of autonomous technologies.
View Blueprint
Improve Healthcare Technology Outsourcing Success
Leading practices and considerations for outsourcing IT to managed service providers.
View Blueprint
Generative AI in Digital Twins
Explore opportunities to enhance precision, predictability, and progress in the manufacturing industry.
View Blueprint
Conduct an AI Privacy Risk Assessment
Navigate AI privacy and data concerns with a comprehensive privacy impact assessment.
View Blueprint
Practical Use Cases for AI in Fleet Management
Using AI to turbocharge your fleet management services.
View Blueprint
Visualize the IT Operating Model
Demonstrate how IT continuously enables value for the organization.
View Blueprint
Life and Annuity Insurance Industry Business Reference Architecture
Business capability maps, value streams, and strategy maps for the insurance industry.
View Blueprint
Virtual Health Playbook: Evaluate and Expand a Virtual Health Practice
Go virtual to increase revenue, expand care options, and improve patient satisfaction.
View Blueprint
Applications Priorities 2024
Five initiatives that help applications leaders optimize their application portfolio and teams in 2024.
View Blueprint
Infrastructure & Operations Priorities 2024
Approach innovation and change with realism and responsibility.
View Blueprint
Security Priorities 2024
Prepare your organization to respond to an evolving threat landscape.
View Blueprint
Develop and Implement a Security Incident Management Program
Create a scalable incident response program without breaking the bank.
View Blueprint
Technology Service Provider Industry Business Reference Architecture
Your guide to building business capability maps, value streams, and strategy maps in the technology service provider industry.
View Blueprint
Build a Data Architecture Roadmap
Optimizing data architecture requires a plan, not just a data model.
View Blueprint
Design Your IT Organization for the Future
Deliver on your most critical objectives with a strategically aligned IT structure.
View Blueprint
Leverage Gen AI to Improve Your Test Automation Strategy
Create an exponential return by integrating AI-enhanced practices into your quality assurance program.
View Blueprint
Manage Your Capacity to Increase Your Availability
Maximize availability through proactive capacity management.
View Blueprint
Optimize IT Governance for Dynamic Decision-Making
Optimize governance to align with how your organization functions.
View Blueprint
Exponential IT Keynote
As technology moves exponentially, so must your entire organization – led by IT.
View Blueprint
Evolve Your Software Development Lifecycle Into a Solution Delivery Lifecycle
It’s "solution delivery," not "software development."
View Blueprint
Align Backups With Your Data Protection Requirements
Making a copy of your data does not always result in data protection.
View Blueprint
Implement Hardware Asset Management
Build a process to track assets across their entire lifecycle.
View Blueprint
Build a Service Desk Consolidation Strategy
A consolidated service desk not only drives more efficient service but is the foundation for optimization and innovation.
View Blueprint
Get Started With AI in Requirements Management
Leverage AI to improve your requirements practices, not replace them.
View Blueprint
Build a Regular CEO IT Update Package
Be prepared for your most important meetings with your most important stakeholder.
View Blueprint
Higher Education Industry Reference Architecture
Business capability maps, value streams, strategy maps, solution architectures, and a catalog of resources for higher education.
View Blueprint
Insurtech Innovations Buyers Guide
Insurtechs are driving the future of the insurance industry.
View Blueprint
Take a Holistic Approach to IT Financial Management
Foster meaningful conversations about IT spending to drive the best business decisions.
View Blueprint
Build a Data-Driven Workforce Plan: A Critical CIO Exercise
Take the guesswork out of your IT workforce equation.
View Blueprint
Address Security and Privacy Risks for Generative AI
AI risk mitigation starts with an acceptable use policy.
View Blueprint
Build an Automation Roadmap to Streamline Security Processes
You can’t defend against today’s automated attacks with slow and manual processes.
View Blueprint
Develop a Flexible IT Funding Model
Unlock the right funding for the right initiative at the right time.
View Blueprint
Deliver Customer Value by Building Digital Trust
Trust-enabled digital services are key to successful adoption of rapidly evolving technologies.
View Blueprint
Identify the Impact of Technical Debt on Government Department/Agency IT Operations
Manage technical debt for enhanced government IT performance.
View Blueprint
Business Vision Diagnostic – Annual IT Improvement Program
Convert your Business Vision Diagnostic results into a focused IT program to enhance business satisfaction.
View Blueprint
The Future of Wholesale and Distribution Trends Report
An Industry Strategic Foresight Trends Report
View Blueprint
Lucratively Nurture Your Donors With a Donor Management System
Technology Opportunity Report
View Blueprint
Maximize the Value of IT Across Enterprise Portfolios
Optimize digital portfolios across multiple product or service lines to maximize value for your organization.
View Blueprint
Select a Security Outsourcing Partner
Outsource the right functions to secure your business.
View Blueprint
Improve Ransomware Resilience for Healthcare
Prevent incursions and defend against ransomware attacks.
View Blueprint
Assess Infrastructure Readiness for Digital Transformation
Unlock the full potential of your infrastructure with a digital transformation strategy, and clear the barriers to success.
View Blueprint
Improve IT Team Effectiveness
Implement the four critical factors required for all high-performing teams.
View Blueprint
Build Your IT Cost Optimization Roadmap
Improve cost-to-value in a sustainable manner.
View Blueprint
Establish Effective Security Governance & Management
The key is in stakeholder interactions, not policy and process.
View Blueprint
Develop Your Value-First Business Process Automation Strategy
As you scale your business automations, focus on what matters most.
View Blueprint
Design and Implement a Business-Aligned Security Program
Focus first on business value.
View Blueprint
Develop a Master Data Management Practice and Platform
Are you sure you have a master data problem?
View Blueprint
Using Supply Chain Control Tower for Competitive Differentiation
Implement a supply chain control tower and put your worries to rest.
View Blueprint
Build a Strategic Infrastructure Roadmap
Building a strategic infrastructure roadmap is a business-driven exercise, not just a technical one.
View Blueprint
Achieve IT Spend & Staffing Transparency
Lay a foundation for meaningful conversations with the business.
View Blueprint
Establish High-Value IT Performance Dashboards and Metrics
Spend less time struggling with visuals and more time communicating about what matters to your executives.
View Blueprint
Set Meaningful Employee Performance Measures
Set holistic measures to inspire employee performance.
View Blueprint
Understand Sustainability Compliance in Chemical Manufacturing
Revolutionize chemical manufacturing and simplify sustainability reporting.
View Blueprint
Effective IT Communications
Empower IT employees to communicate well with any stakeholder across the organization.
View Blueprint
Maximize the Frontline Experience: The Human Side of Technology in Policing
Focus on human-centered design to enhance the frontline experience.
View Blueprint
Addressing the Cybersecurity Talent Shortage in Government
The role of culture, workforce development strategy, and AI in maturing security programs within federal government departments and agencies.
View Blueprint
Understand the IT Implications for the Enrollment Cliff
What is IT’s role in this top priority?
View Blueprint
Leverage Digital Signage for a Better Passenger Experience
Build customer loyalty with immersive passenger experiences.
View Blueprint
Present Security to Executive Stakeholders
Learn how to communicate security effectively to obtain support from decision makers.
View Blueprint
Build an IT Risk Taxonomy
If integrated risk is your destination, your IT risk taxonomy is the road to get you there.
View Blueprint
Mainframe Modernization for Retail Banking
A strategy for modernizing mainframe systems to meet the needs of modern retail banking.
View Blueprint
Non-Durable Goods Manufacturing Industry Reference Architecture
Business capability maps, value streams, and strategy maps for the non-durable goods manufacturing industry.
View Blueprint
Establish a Sustainable ESG Reporting Program
Strengthen corporate performance by implementing a holistic and proactive ESG reporting framework.
View Blueprint
Navigate the Digital ID Ecosystem to Enhance Customer Experience
Beyond the hype: How can it help you become more customer-focused?
View Blueprint
Develop a Targeted Flexible Work Program for IT
Select flexible work options that balance organizational and employee needs to drive engagement and improve attraction and retention.
View Blueprint
Build Your Enterprise Application Implementation Playbook
Your implementation doesn’t start with technology, but with an effective plan that the team can align on.
View Blueprint
Formalize Your Digital Business Strategy
Stay relevant in an evolving digital economy.
View Blueprint
Embrace the Inevitability of Multicloud
The heterogeneous ecosystem is worth it; you just need a cohesive strategy.
View Blueprint
How CIOs Can Get Manufacturing Demand Planning Right
Optimize demand planning to meet rapidly evolving customer needs.
View Blueprint
Enable the Next-Generation Goods Transportation Management System
The time for transportation and logistics companies to modernize their TMS solutions is now.
View Blueprint
Enable the Next-Generation Passenger Transit Management System
The time for transit companies to modernize their TMS solutions is now.
View Blueprint
Leveraging AI to Create Meaningful Insights and Visibility in Retail
AI prominence across the enterprise value chain
View Blueprint
Assess Your Cybersecurity Insurance Policy
Adapt to changes in the cyber insurance market.
View Blueprint
Hire or Develop a World-Class CISO
Find a strategic and security-focused champion for your business.
View Blueprint
Discover the Building Blocks of a Unified Ecosystem
Leveraging hyper-scale technology platforms to enhance the value of services.
View Blueprint
State of Hybrid Work in IT
When tech giants can’t agree and best practices change by the minute, forge your own path to your next normal.
View Blueprint
The State of Black Professionals in Tech
Keep inclusion at the forefront to gain the benefits from diversity.
View Blueprint
The Small Enterprise Guide to People and Resource Management
Quickly start getting the right people, with the right skills, at the right time.
View Blueprint
Harness Configuration Management Superpowers
Create a configuration management practice that will provide ongoing value to the organization.
View Blueprint
CIO Priorities 2023
Engage cross-functional leadership to seize opportunity while protecting the organization from volatility.
View Blueprint
Infrastructure and Operations Priorities 2023
Navigate the liminal space between threats and opportunities.
View Blueprint
Build Resilience Against Ransomware Attacks
Prevent ransomware incursions and defend against ransomware attacks.
View Blueprint
Grid Modernization – Optimize Opportunities and Minimize Risks
Buckle-up for the acceleration in electric utilities.
View Blueprint
Take Action on Service Desk Customer Feedback
Drive up CSAT scores by asking the right questions and effectively responding to user feedback.
View Blueprint
Re-Envision Enterprise Printing
Don’t settle for printer consolidation; seek the elimination of print.
View Blueprint
Define Requirements for Outsourcing the Service Desk
Prepare your RFP for long-term success, not short-term gains.
View Blueprint
Elevate Your Vendor Management Initiative
Transform your VMI from tactical to strategic to maximize its impact and value.
View Blueprint
Make Your IT Governance Adaptable – Financial Services
Build agility into your governance to stay in pace with change.
View Blueprint
Utilities Industry Business Reference Architecture
Business capability maps, value streams, and strategy maps for the electricity, natural gas, water and wastewater utility industries.
View Blueprint
Choose Your Mobile Platform and Tools
Maximize the value of your mobile investments by prioritizing technology decisions on user experience, business priorities, and system quality.
View Blueprint
Optimize Your Loyalty Program Through a Digital Strategy
An industry digital strategy opportunity report
View Blueprint
Develop and Deploy Security Policies
Enhance your overall security posture with a defensible and prescriptive policy suite.
View Blueprint
Build an ITSM Tool Implementation Plan
Plan ahead with a step-by-step approach to ensure the tool delivers business value.
View Blueprint
Support a Data-Driven Student Retention Program
Student success is institutional success.
View Blueprint
Shopping in the Metaverse
Identify and understand the metaverse commerce shopping impacts on retail value streams.
View Blueprint
The ESG Imperative and Its Impact on Organizations
Enable an active response to changing conditions.
View Blueprint
Public Health Practice Business Reference Architecture
Business capability maps, value streams, strategy maps, solution architectures for enterprise architects, and a catalog of resources for public health practice.
View Blueprint
Factory of the Future – Smart Factory Trends for Durable Goods
An industry strategic foresight trends report
View Blueprint
Build a Service-Based Security Resourcing Plan
Every security program is unique; resourcing allocations should reflect this.
View Blueprint
Build an Effective Data Retention Program
Treat the data risks that will derail your retention schedule
View Blueprint
Get the Most Out of Your SAP
In today’s connected world, continuous optimization of enterprise applications to realize your digital strategy is key.
View Blueprint
Get the Most Out of Workday
In today’s connected world, continuous optimization of enterprise applications to realize your digital strategy is key.
View Blueprint
Jump Start Your Vendor Management Initiative
Create and implement a vendor management framework to begin obtaining measurable results in 90 days.
View Blueprint
Durable Goods Industry Business Reference Architecture
Capability maps, value streams, and strategy maps for durable goods manufacturers.
View Blueprint
Build a Zero Trust Roadmap
Leverage an iterative and repeatable process to apply zero trust to your organization.
View Blueprint
Secure Operations in High-Risk Jurisdictions
Security assessments often omit jurisdictional risks. Are your assets exposed?
View Blueprint
Recruit and Retain More Women in IT
Gender diversity is directly correlated to IT performance.
View Blueprint
Create and Implement an IoT Strategy
IT leaders play a key role in implementing IoT successfully.
View Blueprint
Enterprise Architecture Trends
Supporting executives to digitally transform the organization while realizing additional efficiencies at the enterprise level.
View Blueprint
Private Equity and Venture Capital Industry Business Reference Architecture
Business capability maps, value streams, and strategy maps for the Private Equity and Venture Capital Industry.
View Blueprint
Develop an IT Asset Management Strategy
Define your business-aligned approach to ITAM.
View Blueprint
Sports League Business Reference Architecture
Business Capability Maps, Value Streams, and Strategy Maps for Sports Leagues.
View Blueprint
Healthcare Services Industry Business Reference Architecture
Capability maps, value streams, and strategy maps for healthcare services organizations.
View Blueprint
Reshaping the Ecosystem for Industry 4.0 & Industry Next
An industry strategic foresight trends report
View Blueprint
Drive Business Value With Off-the-Shelf AI
A practical guide to ensure return on your off-the-shelf AI investment
View Blueprint
Satisfy Digital End Users With Low- and No-Code
Extend IT, automation, and digital capabilities to the business with the right tools, good governance, and trusted organizational relationships.
View Blueprint
Drive Successful Sourcing Outcomes With a Robust RFP Process
Leverage your vendor sourcing process to get better results.
View Blueprint
Build an IT Risk Management Program
Mitigate the IT risks that could negatively impact your organization.
View Blueprint
Accelerate Through Digital Fan Engagement
An Industry Digital Strategy Opportunity Report
View Blueprint
Prepare an Actionable Roadmap for Your PMO
Turn planning into action with a realistic PMO timeline.
View Blueprint
IT Talent Trends 2022
The last two years were a great experiment … but it’s not over yet. Incorporate new ways of working into your business to build and keep the best team.
View Blueprint
Sports Entertainment Industry Business Reference Architecture
Capability maps, value streams, and strategy maps for sports entertainment organizations.
View Blueprint
Build a Winning Business Process Automation Playbook
Optimize and automate your business processes with a user-centric approach.
View Blueprint
Infrastructure & Operations Priorities 2022
Benefit realization, resource, and risk optimization for I&O leaders
View Blueprint
Make Your IT Governance Adaptable
Governance isn’t optional, so keep it simple and make it flexible.
View Blueprint
Reduce Risk With Rock-Solid Service-Level Agreements
Hold service providers more accountable to their contractual obligations with meaningful SLA components and remedies.
View Blueprint
Health Insurance Industry Reference Architecture
Capability maps, value streams, and strategy maps for health insurance organizations.
View Blueprint
Make the Case for a Room-as-a-Platform Initiative
An industry strategic foresight trends report
View Blueprint
Discover High-Value Fan Experiences
Keep sports fans loyal and engaged in the game by transforming the experience with technology.
View Blueprint
Assess and Govern Identity Security
Strong identity security and governance are the keys to the zero-trust future.
View Blueprint
Define Your Digital Business Strategy
After a major crisis, find your place in the digital economy.
View Blueprint
Determine the Future of Microsoft Project in Your Organization
View your task management, project management, and project portfolio management options through the lens of M365.
View Blueprint
Mergers & Acquisitions: The Sell Blueprint
For IT leaders who want to have a role in the transaction process when their business is engaging in an M&A sale or divestiture.
View Blueprint
Mergers & Acquisitions: The Buy Blueprint
For IT executives who want to be a leader in the M&A transaction process when their business is pursuing a potential acquisition.
View Blueprint
Mature Your Privacy Operations
You’ve mastered the basics, but there are additional risk, data, and measurement tasks to complete.
View Blueprint
Hospital Industry Reference Architecture
Capability maps, value streams, and strategy maps for hospitals.
View Blueprint
Modernize Lottery Channels Through iLottery Selection
Leverage iLottery to modernize lottery channels, allowing your organization to reach more players and drive more revenue.
View Blueprint
Embrace a Sportsbook to Drive Fan Experience and Engagement
Unlocking revenue and fan opportunities through sports betting.
View Blueprint
Integrated Casino Industry Reference Architecture
Capability maps, value streams, and strategy maps for integrated casinos.
View Blueprint
Understand the Data and Analytics Landscape
Optimize your data and analytics environment.
View Blueprint
Hotel Industry Reference Architecture
Capability maps, value streams, and strategy maps for hotels.
View Blueprint
Get the Most Out of Your HRMS
In today’s connected world, continuous optimization of enterprise applications to realize your digital strategy is key.
View Blueprint
Mentoring for Agile Teams
Because Agile transformations can be difficult to navigate on your own.
View Blueprint
Embed Privacy and Security Culture Within Your Organization
Drive employee engagement with privacy and security via governance and process integration.
View Blueprint
Increase Grant Application Success
Enhance your organization's grant writing process.
View Blueprint
Automate Testing to Get More Done
Drive software delivery throughput and quality confidence by extending your automation test coverage.
View Blueprint
Implement Risk-Based Vulnerability Management
Get off the patching merry-go-round and start mitigating risk!
View Blueprint
Get the Most Out of Your ERP
In today’s connected world, the continuous optimization of enterprise applications to realize your digital strategy is key.
View Blueprint
Embrace Cashless in Your Casino
Prepare for the inevitable adoption and implementation of a virtual wallet.
View Blueprint
Create a Work-From-Anywhere Strategy
Ensure short-term survivability while working toward near-term innovation.
View Blueprint
Identify the Components of Your Cloud Security Architecture
Security in the cloud requires solutions, not speculation.
View Blueprint
Build a Chatbot Proof of Concept
Create value for your business with your chatbot implementation.
View Blueprint
Win More Grant Funding Opportunities
Enhance your tribal nation’s grant application process.
View Blueprint
Master the Public Cloud IaaS Acquisition Models
Technically, most platforms are similar; however, their procurement models vary significantly. Learn the differences, save on costs, and reduce risk.
View Blueprint
Take Control of Cloud Costs on AWS
Change the way you work to get full value from the cloud.
View Blueprint
Kick-Start an Esports Initiative at Your Casino
Esports initiative success depends on achieving integration into the existing casino ecosystem.
View Blueprint
Create an IT View of the Service Catalog
Unlock the full value of your service catalog with technical components.
View Blueprint
Kick-Start IT-Led Business Innovation
Innovate now – formalize later! Digital transformation won't wait.
View Blueprint
Implement Desktop Virtualization and Transition to Everything as a Service
From VDI to DaaS, desktop virtualization is back. Choose the right solution, then develop an implementation plan that balances user experience, infrastructure complexity, and total cost.
View Blueprint
Build or Refresh the WLAN
Don’t gamble with your wireless network; enhance guest experience with an efficient and reliable WLAN.
View Blueprint
Establish a Service-Based Costing Model
Not knowing your costs is an expense you can’t afford.
View Blueprint
Outsource IT Infrastructure to Improve System Availability, Reliability, and Recovery
There are very few IT infrastructure components you should be housing internally – outsource everything else.
View Blueprint
Create a Game Plan to Implement Cloud Backup the Right Way
Optimize your backup initiative and mitigate the challenges of the cloud.
View Blueprint