Can a Vendor Management Initiative Influence Organizational Performance?
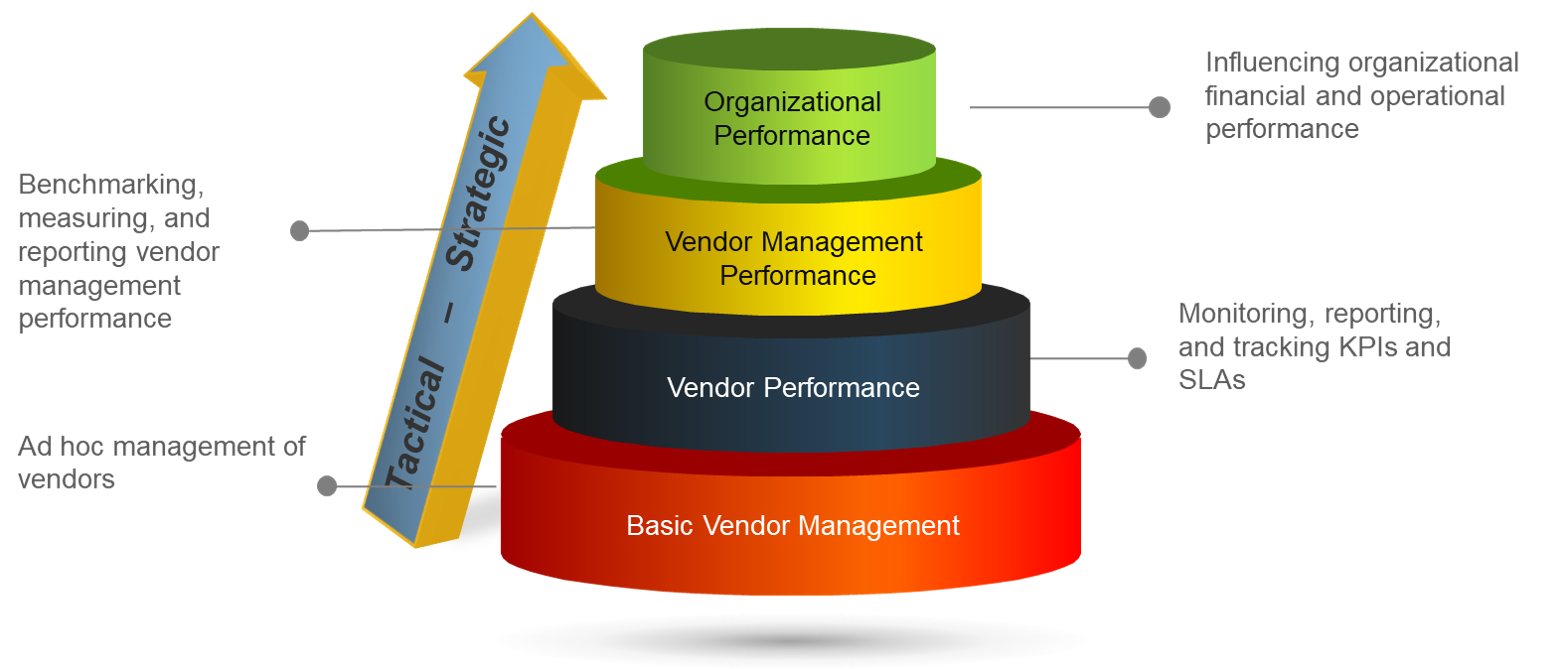
Can a vendor management initiative influence organizational performance? The concise answer to this question is yes. However, this influence doesn’t occur overnight. Your vendor management initiative must progress through four levels of influence from tactical to strategic to achieve organizational impact. Exploring Info-Tech’s Four Levels of Vendor Management Performance will guide you through your vendor management initiative’s maturation of organizational influence.
The Four Levels of Vendor Management Performance are:
- Basic Vendor Management
- Vendor Performance
- Vendor Management Performance
- Organizational Performance
Basic Vendor Management
Starting with the Basic Vendor Management level, the vendor management team must identify opportunities and execute tactical fundamentals of vendor management. These tactical fundamentals typically include contract negotiations, contract management, spend analytics, and routine sourcing activities.
Vendor Performance
Monitoring vendor performance is the next level in our progression of influence. The vendor management team needs to perform vendor service level agreement/objectives (SLA/SLO) monitoring with periodic business reviews along with market intelligence/benchmarks to influence the vendors' performance.
Vendor Management Performance
Upon establishing competencies at the Vendor Performance level, the vendor management team needs to perform self-evaluation by examining how well the vendor management team is performing. Measuring the team’s performance in areas such as value creation, the quantity of negotiated contracts, spend addressed, and vendor management return on investment will provide insight into the opportunities for improvement and successful accomplishments to highlight.
Organizational Performance
The ultimate aspirational level of the vendor management team is influencing their organization’s operational and financial performance. Leveraging the vendor management team’s knowledge and fluctuations in the market place allows the team to influence the organization’s IT strategy and architecture and even the organization’s products and services. The vendor management team’s success in cost reductions, improving efficiencies, and value creation will contribute to the organization’s financial performance.
The graphic below summarizes the Four Levels of Vendor Management Performance explored above.
Four Levels of Vendor Management Performance
Our Take
A significant amount of an organization’s decisions involves information provided by IT. Thus, a highly competent, experienced vendor management team should aspire to influence the operations and financial performance of their organization by being a business solution architect that is a trusted advisor for IT strategy that drives business value by improving operational and financial performance. Understanding the Four Levels of Vendor Management Performance will establish your vendor management initiative in an optimal position to influence the operational and financial performance of the organization.
Want to Know More?
Manage Your Vendors Before They Manage You









