As cyber threats against the U.S. Defense Industrial Base increase, the Department of Defense (DoD) now requires its contractors and subcontractors to clearly define, protect, and prove how Controlled Unclassified Information (CUI) is handled within their environments. But updated Cybersecurity Maturity Model Certification (CMMC) 2.0 requirements leave CIOs and CISOs unsure what they need to do next or how to prepare for an audit. This blueprint helps organizations take a structured approach to CMMC readiness by validating scope, clarifying roles and responsibilities, and ensuring technical controls are supported by documented policies, repeatable processes, and defensible evidence.
Many organizations are discovering that technical security maturity alone is not sufficient to meet updated CMMC requirements. While security tools and configurations may be in place, gaps in governance, documentation, and organizational alignment make it difficult to demonstrate CMMC compliance. Without clear scope, supporting evidence, and documented processes, organizations risk failing their assessment despite having implemented controls.
1. Instead of securing the whole house, just lock the vault.
Isolate CMMC-regulated information in a controlled environment to achieve compliance faster, reduce costs, and minimize risk without overhauling the entire IT ecosystem. By containing CUI within defined enclaves, organizations can reduce the scope of assessment and simplify how they demonstrate compliance.
2. Scoping is the first control.
Many organizations underestimate how critical proper scoping is to CMMC. By focusing early on defining the right system boundaries and using enclaves to contain CUI, organizations can reduce assessment complexity, limit risk exposure, and manage compliance costs more effectively.
3. Readiness planning should start with the end in mind.
Starting with a target timeline and working backward allows organizations to frame CMMC readiness as a structured project. This approach helps establish milestones, assign resources, and align remediation activities within stipulated timeframes.
Use this step-by-step blueprint to prepare for a CMMC audit with confidence.
Our research helps organizations accelerate time to certification with practical templates and tools, including a communication deck, asset inventory tool, readiness assessment tool, and system security plan template. Organizations can also leverage our workshops for hands-on support in baselining current state, developing key deliverables, and preparing for audit.
Use our four-phase approach to:
- Define CMMC scope by identifying CUI system boundaries to limit the assessment footprint.
- Assess current-state CMMC compliance by evaluating how requirements are implemented across in-scope systems, services, and assets.
- Translate assessment findings into an actionable CMMC audit readiness roadmap by prioritizing remediation initiatives and sequencing them into an executable plan.
- Validate that remediation efforts have been effectively implemented and that CMMC controls are operating as intended to protect CUI.
Assess Your CMMC Readiness
Secure what matters to fast-track CMMC compliance.
Analyst perspective
Take a structured approach to Cybersecurity Maturity Model Certification.
Cyber threats against the defense industrial base continues to increase. The Department of Defense (DoD) now requires organizations to clearly define, protect, and prove how Controlled Unclassified Information (CUI) is handled within their environments. The Cybersecurity Maturity Model Certification (CMMC) 2.0 is no longer a future requirement, it demands substantial effort and preparation.
Many organizations are discovering that technical security maturity alone is not sufficient. While security tools and configurations may be in place, gaps in governance, documentation, and organizational alignment often create risks. Organizations that approach CMMC readiness proactively reduce this risk by assessing their posture before engaging a formal certification process.
A structured readiness assessment allows organizations to validate scope, clarify roles and responsibilities, and ensure that technical controls are supported by documented policies, repeatable processes, and defensible evidence.
By treating readiness as a preparatory phase rather than a checkpoint, organizations improve accountability, reduce assessment uncertainty, and strengthen their ability to meet contractual obligations. This blueprint will help organizations focus effort where it matters most and accelerate time to certification.

Safayat Moahamad
Research Director
Security and Privacy
Info-Tech Research Group
Executive summary
Your Challenge |
Common Obstacles |
Info-Tech’s Approach |
|---|---|---|
Becoming CMMC ready with clear visibility. Organizations often lack a clear understanding of what falls within scope and where controls must be implemented. Aligning the enterprise around CMMC readiness. CMMC may be perceived as a compliance-driven exercise. Gaining ownership across the business is difficult. Preparing for assessment with confidence. Not validating CMMC readiness increases the risk of assessment delays, unexpected findings, and costly remediation under time pressure. |
Poorly defined scope and system boundaries. Overly broad or unclear scoping expands the assessment footprint and increases costs. Disconnected controls, documentation, and evidence. Technical controls may exist, but policies, procedures, and evidence are often incomplete, inconsistent, or misaligned with assessor expectations. Limited enterprise engagement and accountability. Without clear roles, ownership, and shared understanding, CMMC readiness stalls. Business units may resist participation. |
Start with precise scoping. Define CUI system boundaries to limit assessment complexity and reduce risk exposure. Conduct a tailored CMMC readiness assessment. Evaluate technical controls, governance, documentation, and evidence against CMMC requirements to identify true readiness gaps. Deliver a practical roadmap to certification readiness. Translate assessment findings into a prioritized, role-based roadmap with clear ownership, timelines, and next steps to prepare confidently for certification. |
Info-Tech Insight
Scoping is the first control. Many organizations underestimate how critical proper scoping is to CMMC compliance. By focusing early on defining the right system boundaries and using enclaves to contain CUI, organizations can reduce assessment complexity, limit risk exposure, and manage compliance costs more effectively.
Cybersecurity Maturity Model Certification
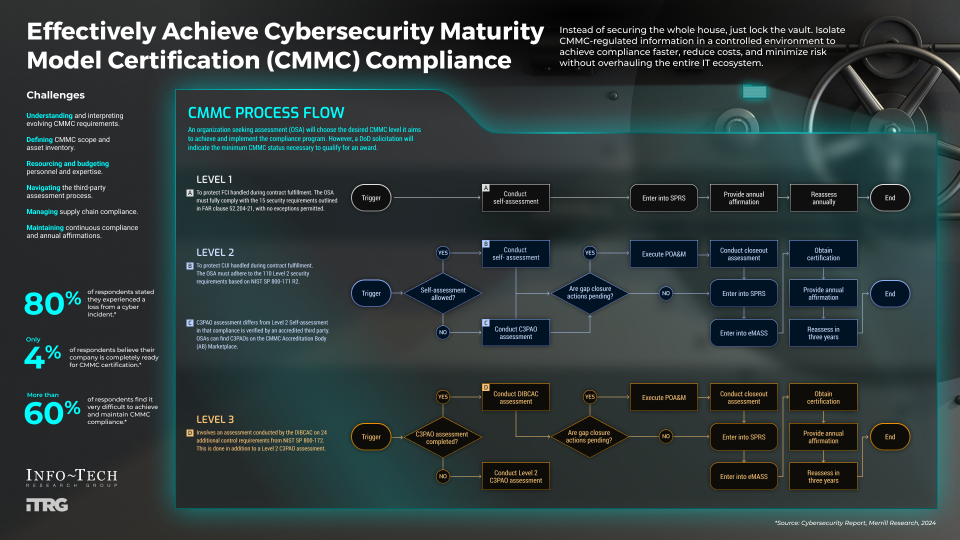
The CMMC is a mandatory compliance requirement for the US Department of Defense (DoD) contractors and subcontractors. The framework is aimed to ensure protection of Federal Contract Information (FCI) and Controlled Unclassified Information (CUI).
The Defense Industrial Base (DIB) experiences frequent and complex cyberattacks. The CMMC mandates that companies managing sensitive DoD information adopt increasingly sophisticated cybersecurity measures.
Through CMMC assessments, the DoD ensures compliance with these standards. Consequently, DoD contractors and subcontractors must meet a designated CMMC level to be eligible for contract awards.
CMMC Level |
Controls |
Assessor |
Applicability |
LEVEL 1 |
15 |
Self |
All DoD Contractors |
LEVEL 2 |
110 |
Self or Accredited Third Party 1 2 |
Contractors Handling CUI |
LEVEL 3 |
134 |
DIB Cybersecurity Assessment Center |
Critical Defense Programs |
2 Accredited Third Party = Certified Third-Party Assessor Organization (C3PAO)
Info-Tech Insight
Defining the right CMMC assessment scope is critical. Strategically enclave your architecture and the boundary of certification to balance requirements with security, efficiency, and cost considerations.
Your challenge
This research is designed to help organizations who are facing these challenges:
- Understanding and interpreting evolving CMMC requirements
- Accurately defining CMMC scope and asset inventory
- Resource constraints, such as budget, personnel, and expertise
- Navigating the third-party assessment process
- Managing supply chain compliance
- Maintaining continuous compliance and annual affirmations
“DoD will include CMMC requirements in solicitations and contracts. Contractors who process, store, or transmit FCI or CUI must achieve the appropriate level of CMMC as a condition of contract award.”
– Pentagon qtd. in DefenseScoop, 2024
80% of respondents stated they experienced a loss from a cyber incident.
Only 4% of respondents believe their company is completely ready for CMMC certification.
More than 60% of respondents find it very difficult to achieve and maintain CMMC compliance.
Source: Merrill Research, 2024
Common obstacles
These barriers are challenging for many organizations:
- Lack of executive buy-in and organizational alignment
- Unclear roles and responsibilities for CMMC implementation
- Vendor and external service provider (ESP) dependencies
- Legacy IT systems and technical debt
- Complicated and time-consuming assessment preparation
- Unclear path for organizations moving from Level 2 to Level 3
“We continuously have our data taken by advanced persistent threats. We have contractors that get targeted by malicious actors trying to extort money.”
– Stacy Bostjanick, chief of defense industrial base cybersecurity, qtd. in “DOD Simplifies Process for Defense Contractors,” US Department of Defense, 2024
Less than 40% are actively working on SSPs, POAMs, required controls, and ongoing compliance plans.
Over 50% highlighted significant cost impacts due to ongoing changes and necessary tools.
Approximately 40% rated DFARS reporting an 8 out of 10 or higher in terms of difficulty.
Source: Merrill Research, 2024
Insight summary
Secure what matters to fast-track CMMC compliance.
Scoping is the first control.
Scoping is the first control. Many organizations underestimate how critical proper scoping is to CMMC compliance. By focusing early on defining the right system boundaries and using enclaves to contain CUI, organizations can reduce assessment complexity, limit risk exposure, and manage compliance costs more effectively.
Subcontractor obligations are often overlooked.
Prime contractors are must ensure that subcontractors handling CUI also meet CMMC requirements.
Audit success depends on evidence.
Strong security practices alone are not enough. Organizations must maintain clear, verifiable documentation such as the System Security Plan (SSP), the Plan of Action and Milestones (POA&M), and mapped policies to demonstrate compliance during assessments.
Readiness planning should start with the end in mind.
Starting with a target timeline and working backward allows organizations to frame CMMC readiness as a structured project. This approach helps establish milestones, assign resources, and align remediation activities within stipulated timeframes.
Capture treatment of asset categories by control and defined responsibility.
Readiness often stalls when control implementation plans are not well documented to reflect ownership and objectives.
Blueprint benefits
IT Benefits |
Business Benefits |
|---|---|
|
|
The Key Deliverable
CMMC Readiness Communication Deck
Use this deck to consolidate readiness findings, communicate scope and risks, and align stakeholders. The deck translates technical and compliance insights into clear, executive-ready messaging to support enterprise engagement.
Leverage these supporting tools to inform the key deliverable:
CMMC Asset Inventory Tool
Establish visibility into in-scope assets by identifying systems, applications, users, and data that store, process, or transmit CUI.
CMMC Readiness Assessment Tool
Assess current-state readiness, identify gaps, and prioritize remediation activities before entering formal certification process.
System Security Plan Template
Use the SSP to demonstrate how CMMC requirements are implemented and maintained within the defined scope.

 Assess and Manage Security Risks
Assess and Manage Security Risks
 Assess Your Cybersecurity Insurance Policy
Assess Your Cybersecurity Insurance Policy
 Achieve Digital Resilience by Managing Digital Risk
Achieve Digital Resilience by Managing Digital Risk
 Prevent Data Loss Across Cloud and Hybrid Environments
Prevent Data Loss Across Cloud and Hybrid Environments
 Build an IT Risk Management Program
Build an IT Risk Management Program
 Develop and Deploy Security Policies
Develop and Deploy Security Policies
 Fast Track Your GDPR Compliance Efforts
Fast Track Your GDPR Compliance Efforts
 Build a Security Compliance Program
Build a Security Compliance Program
 Embed Privacy and Security Culture Within Your Organization
Embed Privacy and Security Culture Within Your Organization
 Establish Effective Security Governance & Management
Establish Effective Security Governance & Management
 Improve Security Governance With a Security Steering Committee
Improve Security Governance With a Security Steering Committee
 Develop Necessary Documentation for GDPR Compliance
Develop Necessary Documentation for GDPR Compliance
 Reduce and Manage Your Organization’s Insider Threat Risk
Reduce and Manage Your Organization’s Insider Threat Risk
 Satisfy Customer Requirements for Information Security
Satisfy Customer Requirements for Information Security
 Master M&A Cybersecurity Due Diligence
Master M&A Cybersecurity Due Diligence
 Integrate IT Risk Into Enterprise Risk
Integrate IT Risk Into Enterprise Risk
 Present Security to Executive Stakeholders
Present Security to Executive Stakeholders
 Deliver Customer Value by Building Digital Trust
Deliver Customer Value by Building Digital Trust
 Address Security and Privacy Risks for Generative AI
Address Security and Privacy Risks for Generative AI
 Protect Your Organization's Online Reputation
Protect Your Organization's Online Reputation
 Develop an AI Compliance Strategy
Develop an AI Compliance Strategy
 Get Started With AI Red-Teaming
Get Started With AI Red-Teaming
 Achieve CMMC Compliance Effectively
Achieve CMMC Compliance Effectively
 Building Info-Tech’s Chatbot
Building Info-Tech’s Chatbot
 Building the Road to Governing Digital Intelligence
Building the Road to Governing Digital Intelligence
 An Operational Framework for Rolling Out AI
An Operational Framework for Rolling Out AI
 Discover and Classify Your Data
Discover and Classify Your Data
 Defend Against Deepfake Cyberattacks
Defend Against Deepfake Cyberattacks
 Assess Your CMMC Readiness
Assess Your CMMC Readiness