An IT leader in a growing municipality needs to take a proactive approach to security and build out its policies. Info-Tech’s blueprints and templates save them time and effort.
Situation: A small municipality is growing quickly and adding services. IT has a broad range of coverage, including support for emergency services, GIS, and operational technology (OT) for waste water management. The municipality recently underwent an AWWA (American Water Works Association) security audit that indicated some deficiencies.
Complication: The IT team has traditionally approached security by addressing the deficiencies found via audits. Counsel, however, wants IT to take a much more proactive role in security and policy development.
Recommendations
- Build an Information Security Strategy. IT leaders that are focusing on IT security need to address two core questions: “how much security do we need?” and “how much security do we have?” These questions can be particularly difficult to answer within the context of different auditing frameworks and approaches (NIST, ISO, etc.). This Info-Tech blueprint introduces a model that maps to these various frameworks and enables IT leaders to assess their capabilities. Important tools include:
- Information Security Pressure Analysis Tool (Excel). This tool enables IT leaders to determine how much security they currently need and if those needs will change in the immediate future.
- Information Security Program Gap Analysis Tool (Excel). This tool answers the second question. It provides a list of questions that leaders answer using a 1-5 scale. It generates a heat map that is valuable for communicating security needs to senior leadership and board-level committees. Importantly, the resulting gaps serve as inputs to shape the portfolio of security projects.
- Align Your Security Controls to Industry Frameworks for Compliance. The model we present in our security strategy blueprint is a composite of various frameworks. This blueprint provides specific guidance on mapping back to NIST, etc. It gives IT leaders – and their auditors – specific guidelines on controls, etc. Use this tool:
- Control Framework Mapping Tool (Excel)
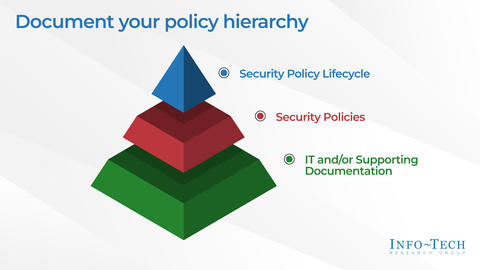
- Identify the Best Framework for Your Security Policies. The last step is to identify specific Info-Tech templates that address the needs identified in the gap analysis tool. This blueprint includes a variety of very common IT policies using NIST- and ISO-specific language.
- Use myPolicies. One of the key challenges of using IT policies is ensuring that they are accessible and that users are familiar with the content. Info-Tech can help with our myPolicies offering. It is included with most of our standard membership packages. Ask your account manager for details.
Bottom Line
Info-Tech’s blueprints and tools are valuable starting points for building out IT security policies.