Traditional cryptography is no longer enough. Public key infrastructure (PKI) processes lack the robustness required to meet the complex challenges of post-quantum computing, AI agents, and shortened certificate lifespans. The real challenge isn’t PKI itself – it's managing the full lifecycle of certificates across a growing digital ecosystem. Use this step-by-step blueprint to adopt certificate lifecycle management (CLM) that’s enabled by automation and designed to build greater security and agility into your organization.
Growing certificate scope and identity sprawl have made the process of certificate enrollment, renewal, and revocation labor-intensive and a prime candidate for automation. With certificate lifespans shrinking from years to months, automation can streamline certificate management and provide the crypto-agility that’s now essential to digital trust. Adopt a consistent CLM framework to automate certificate management, reduce risk, and enhance IT’s ability to adapt to evolving enterprise needs.
1. Don’t DIY your certificate processes.
Use a PKI solution for certificate discovery and management. This technology will typically help with the heavy lifting involved in identifying and managing certificates across your IT infrastructure. Look for capabilities such as network discovery, agent-based discovery, certificate authorities integration, and agentless discovery and analysis.
2. Get ready for post-quantum cryptography.
Quantum computing is coming. New quantum safe signatures will soon be available – and necessary – to maintain cryptographic security. Expect key encapsulation mechanisms (KEM) used in data in transit encryption – like transport layer security (TLS) - to leverage hybrid cryptography, i.e. legacy and post-quantum safe signatures. Consider PQC’s larger storage requirements and current certificate format and size constraints.
3. Build automation into CLM right from the start.
Relying on manual or human-driven processes will leave you with the same problems you face today. Certificate lifespans as short as 47 days are coming, and they’ll be impossible to manage manually. Automating certificate discovery and inventory also gives you the agility to deal quickly with certificate revocations and respond swiftly to shifting business needs.
Use this step-by-step blueprint to adopt CLM for crypto-agility and greater digital trust.
Our research offers a comprehensive storyboard and four complementary, practical tools to transform strategy into actionable steps. Use our four-phase approach to adopt a CLM framework for crypto-agility.
- Observe to inventory and continuously monitor for new certificates and those that are out of compliance. This helps your organization drive standardization and reduce risk.
- Standardize to ensure the right cryptographic strength, identify ownership, and mandate agreed upon policy statements like bit strength and format (SAN, Wildcard). This facilitates integration and enforces CLM.
- Automate to remove human error, drive consistency, and allow your organization to scale CLM.
- Measure program effectiveness and enhance observability to help identify risks and establish a continuous improvement loop.
Member Testimonials
After each Info-Tech experience, we ask our members to quantify the real-time savings, monetary impact, and project improvements our research helped them achieve. See our top member experiences for this blueprint and what our clients have to say.
9.0/10
Overall Impact
$31,960
Average $ Saved
5
Average Days Saved
Client
Experience
Impact
$ Saved
Days Saved
Aipso
Guided Implementation
9/10
$31,960
5
Master Certificate Lifecycle Management
Enable crypto-agility for the security, scalability, and automation to empower your organization’s digital trust.
Executive Summary
Your Challenge
- Certificate scope is growing and time-to-live is shortening – making your labor-intensive enrollment, renewal, and revocation workloads unmanageable.
- Human identities, nonhuman identities, and machine identities continue to sprawl, requiring a robust lifecycle.
- Exponential IT demands like AI agents and post-quantum computing are coming quickly, and maintaining digital trust will demand crypto agility in your processes.
Common Obstacles
- Implementation of certificate lifecycle management (CLM) can be complex involving a multitude of components, technologies, and new skill sets.
- Successful implementation of CLM must address the complexity and the lifecycle process of certificate activities.
- Cradle-to-grave lifecycle processes must be fully vetted before the first certificate is issued.
- Public key infrastructures (PKI) can be difficult to manage and incur significant risk.
Info-Tech’s Approach
- Understand the various PKI architectures available. Select the architecture best suited to your organization and risk tolerance.
- Learn how you can observe, standardize, automate, and measure your CLM program.
- Become familiar with different discovery techniques, CLM protocols, and pitfalls.
- Establish a cycle of ongoing enhancement for your CLM program through consistent measurement.
Info-Tech Insight
Traditional PKI is no longer enough – crypto-agility is what separates brittle IT from flexible and quickly adaptable IT. Certificate lifecycle management is the path to crypto-agility, providing the ability to automate certificate management, update algorithms, keys, and protocols, and to maintain compliance.
Your Challenge
Digital trust is built upon a foundation of robust digital identity that provides strong authentication for users, devices, and applications. Effective certificate management is central to all of this.
- PKI is an essential component to cryptography; however, it’s not enough. Organizations that struggle with managing cryptographic keys don’t have PKI infrastructure issues; they have certificate management issues.
- Standardization and automation play a crucial role in simplifying certificate processes like enrollment, issuance, distribution, renewal, and revocation.
- Machines that have access to your resources have the ability to do a great deal of good – or a great deal of harm.
- For the best security, machine identity authentication should be ubiquitous, and certificates should be short lived.
- Implementing this capability will require a strong certificate management program.
Organizations primarily leverage their own PKI for data encryption
28% of stated encryption is performed on-premises using organizations’ own keys, prior to being sent to the cloud. (Source: Entrust, State of Zero Trust & Encryption Study, 2024)
With certificate lifespans rapidly shortening, organizations will need robust solutions to keep pace
90 days — Google has announced its plans to reduce SSL/TLS certificate validity terms to 90 days in 2026.
47 days — Apple is proposing the further reduction of certificate terms to end with a maximum validity of 47 days by April 2029. (Source: Encrypted Fence (Certera), 2024)
Certificate lifecycle management (CLM) benefits both the business and security
Business Value & Impact
- Effective certificate management prevents application downtime and outages caused by faulty or expired certificates.
- Effective certificate management enables identity access management, web app security, and network protection.
- Automation of certificate processes (enrollment, issuance, distribution, renewal, revocation) simplifies certificate management and reduces human error.
- By preventing breaches and outages, strong CLM reduces financial losses and reputational damage.
- Good CLM promotes trust in online transactions and ensures secure communications.
Key Benefits and Capabilities of PKI for Zero Trust
- Public key cryptography is essential to supporting least privilege and multi-factor authentication (MFA).
- Certificate-based cryptography provides in-transport and at-rest data encryption, ensuring confidentiality and integrity.
- Certificate-based digital signatures for verifying the authenticity of documents and transactions.
- Public key cryptography secures communication between devices, preventing unauthorized access and data tampering.
- Cryptographic data protection is required by industry regulations, such as those governing financial services and healthcare.
- A well-implemented cryptographic lifecycle can help reduce the risk of data breaches and other security incidents.
Adoption & Perception
CLM is not merely a technical component but a foundational element for establishing robust data protection and secure communications. Its business value lies in its ability to enhance security, ensure compliance, reduce operational risks and costs, and enable secure digital transformation.
- Budget Allocation: The Ponemon Institute discovered that enterprises passed a new milestone after 16 years of conducting the Global Encryption Trends Study, with 50% saying that they had an overall encryption strategy that is implemented regularly. (Entrust, 2022)
- Reluctance to Implement: Despite its importance, 61% of companies are not currently using CLM as part of their zero trust strategy. (Sectigo, 2024) This highlights a gap between the recognition of CLM’s importance and its actual implementation.
Certificate lifecycle management is the most important aspect of modern cryptography
Cryptography ≠ PKI. It’s no longer about the infrastructure – organizations succeed or fail based on their ability to manage the complete lifecycle of certificates.
INFO-TECH’S CLM PROGRAM LIFECYCLE
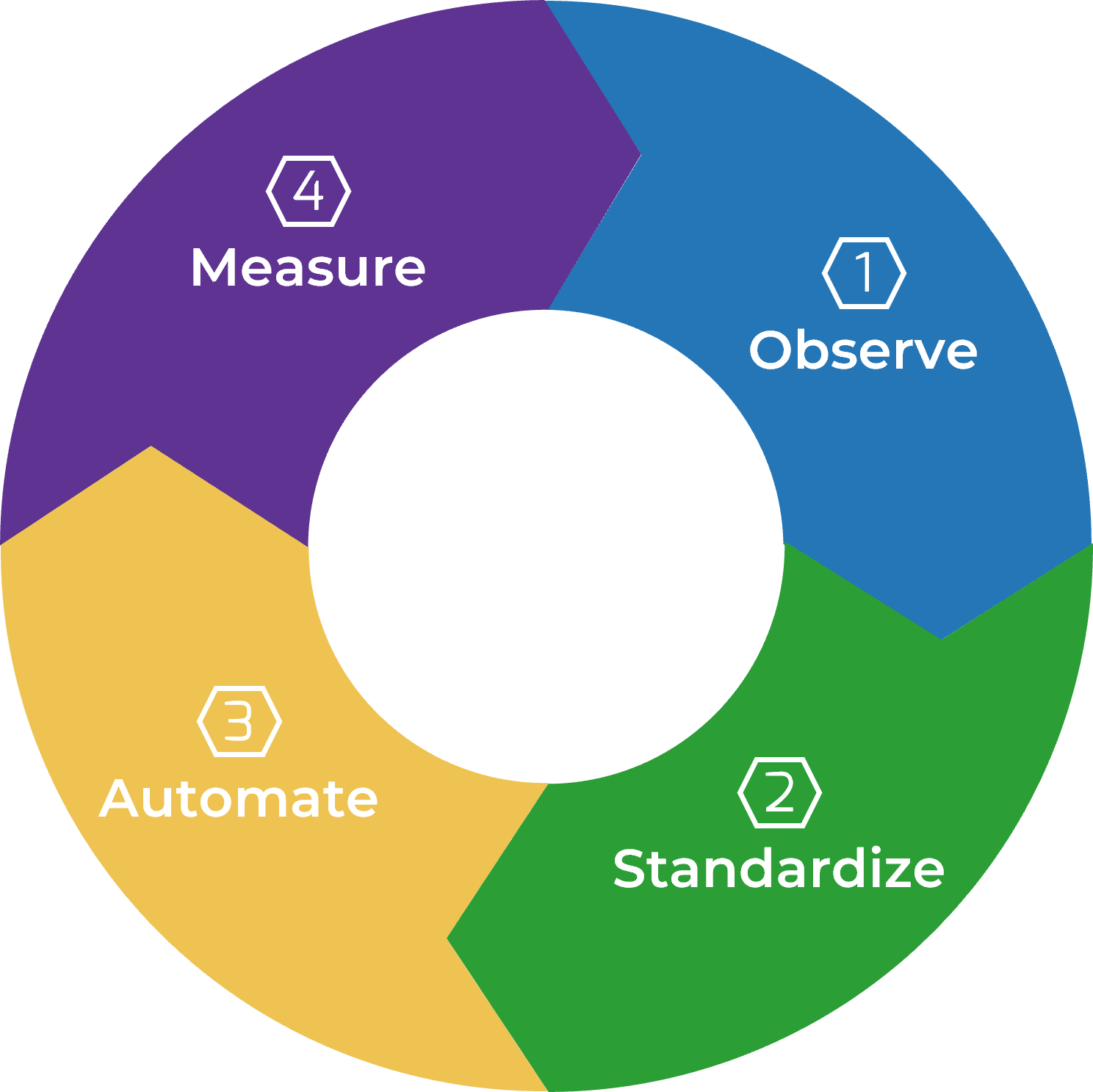
IMPLEMENT THESE FOUR PHASES FOR EFFECTIVE CERTIFICATE MANAGEMENT:
-
Observe
Allows for discovery, monitoring, adding to central inventory, and reporting of your certificate inventory to help your organization drive standardization and reduce risk. Enterprises should continuously monitor for new certificates and those that are out of compliance. -
Standardize
Ensures the right level of cryptography, the ability to identify ownership, and mandates agreed-upon protocols (e.g. ACME, SCEP, CMP, proprietary agent) to facilitate integration and enforce CLM. -
Automate
Removes human error, drives consistency, and allows organizations to scale. It also provides a mechanism to orchestrate certificate rotation/renewal frequently as well as being able to revoke them easily. -
Measure
Measures program effectiveness and enhances observability. Measuring effectiveness by pillar provides data points that help identify risks and establish a continuous improvement loop.
Prerequisites before starting your certificate lifecycle journey
Preparing to build a robust and effective certificate lifecycle management program goes beyond simply implementing systems and processes. It is vital for senior management to receive comprehensive guidance on the challenges, risks, and potential mitigations associated with maintaining a secure and scalable framework.
Education on certificate lifecycle management should be tailored to individuals based on their specific roles and the impact of these systems on their responsibilities. This customized approach ensures that individuals are equipped with the necessary knowledge and skills relevant to their respective roles, enabling the organization to maintain trust, security, and compliance.
Leadership Buy-In
- Secure senior management commitment to cryptographic initiatives.
- Assess the scope of PKI-dependent systems and certificates.
- Set achievable PKI maturity goals and define projects.
Roles and Responsibilities
- Define clear ownership for the certificate lifecycle program.
- Establish a cross-functional cryptography task force.
- Document and communicate role-specific responsibilities.
Awareness and Education
- Educate senior management on CLM’s strategic importance and risks.
- Tailor certificate lifecycle training for different roles.
- Promote ongoing awareness campaigns.
Info-Tech Insight
Invest in tools that support cryptography and certificate lifecycle management, such as automated certificate management platforms that provide visibility into certificate inventories, automate renewals, and integrate with existing systems like Active Directory or cloud platforms (AWS, Azure AD, GCP).
1. OBSERVE
Observation starts with scoping and discovering what you have
Where are you starting from?
- The challenge for most organizations is not that they’re starting from scratch – rather, they have key management activities going on, but they lack maturity and consistency in their practices.
- Since most cases will not be starting from a blank canvas, it’s important to first understand what the current environment looks like.
- Start by investigating your environment to define your scope of key management requirements, and also identify existing cryptography components active today.
Components to look for may include:
- Cloud Environments
- Hardware Security Module (HSM)
- Certificate Authority
- Container Environments
- Applications
- Mobile Device Management (MDM)
- IoT
- Discovery Tools
- SSH key & Certificate Management
- Code Signing
- PKaaS
- Certificate LCM Automation
Info-Tech Insight
Consider supply chain risks. Work with key vendors on a common approach to quantum-safe governance.
Don’t DIY – use technology for PKI certificate discovery and management
A PKI solution will typically help with heavy lifting in discovery
- Certificate discovery capabilities typically revolve around identifying and managing certificates across your IT infrastructure, and they primarily focus on SSL/TLS certificates, used for secure communication.
- Differentiating features in a CLM solution can discover other types of certificates such as those embedded in code or containers.
Capabilities to look for in a comprehensive scanner
- Network discovery:
- Installed on a Linux or Windows machine.
- Discovers certificates on local subnet ranges (RFC 1918) and local hostnames.
- Agent-based discovery: Deploy lightweight agents on endpoints for deeper visibility and certificate management.
- CA integration: Connect directly to certificate authorities (CAs) to discover issued certificates (including Kubernetes CA, often referred to simply as the Cluster CA).
- Agentless method:
- Uses the internet to perform TLS connections to specified IP addresses and hostnames.
- Downloads certificates found during these connections into a certificate manager for inventory.
- Vaulting services:
- Discovers certificates stored in services like Azure Key Vault, AWS, and GCP.
- Integrates these certificates into a certificate manager for comprehensive inventory.
Info-Tech Insight
It’s important that you can send alerts about certificate statuses, expirations, and renewals through various channels like email, Slack, and MS Teams.
Observation is an ongoing process of discovery, inventory, monitoring, and reporting
Discovery
- Comprehensive Scanning
Leverage a discovery tool that performs top-down scans across your entire network to find all certificates and keys and their locations. These scans should occur at regular intervals (e.g. weekly) to identify any new certificates and eliminate undocumented ones. - Locate Certificates
Determine where each certificate is deployed, whether on a firewall, browser, or other endpoints. This ensures no certificate is missed during bulk renewals or revocations. - Smart Discovery
The solution should ideally provide smart discovery features to find more certificates, making certificate lifecycle management quicker and more effective. Discovering certificates across hybrid multicloud infrastructures and integrating with your existing certificate scanner will avoid using multiple scanners.
Inventory
- Centralized Database
Organize all discovered certificates in a central database to gain meaningful insights. This database should automatically maintain a structured inventory with details such as name, expiration date, encryption strength, key strength, network location, etc. - Detailed Information
The inventory should include details such as validity period, certificate type, position in the chain, and location on the network to help avoid outages and fix issues. The inventory should provide a lateral view to easily verify the chain of trust. - Grouping Certificates
Group certificates based on the issuing CA or location to streamline renewals and revocations. The inventory should be customizable, with options to include granular certificate details and metadata. - Single Pane of Glass
A centralized view of certificates and their information helps monitor certificates for vulnerabilities and stay on top of certificate expiry to prevent outages and security threats.

 Privacy by Design for Digital Marketing
Privacy by Design for Digital Marketing
 Build a Data Privacy Program
Build a Data Privacy Program
 Mature Your Privacy Operations
Mature Your Privacy Operations
 Fast Track Your GDPR Compliance Efforts
Fast Track Your GDPR Compliance Efforts
 Secure Your High-Risk Data
Secure Your High-Risk Data
 Ensure Your Pandemic Response Plan Is Privacy-Proof
Ensure Your Pandemic Response Plan Is Privacy-Proof
 Comply With the California Consumer Privacy Act
Comply With the California Consumer Privacy Act
 Build an Effective Data Retention Program
Build an Effective Data Retention Program
 Demonstrate Data Protection by Design for IT Systems
Demonstrate Data Protection by Design for IT Systems
 Tech Trend Update: If Digital Ethics Then Data Equity
Tech Trend Update: If Digital Ethics Then Data Equity
 Conduct an AI Privacy Risk Assessment
Conduct an AI Privacy Risk Assessment
 Prepare for PCI DSS v4.0
Prepare for PCI DSS v4.0
 Comply With the California Privacy Rights Act
Comply With the California Privacy Rights Act
 Comply With 2023 US Privacy Laws (Virginia, Connecticut, Utah, Colorado)
Comply With 2023 US Privacy Laws (Virginia, Connecticut, Utah, Colorado)
 Master Certificate Lifecycle Management
Master Certificate Lifecycle Management