Rapid changes to security and compliance requirements are outpacing many organizations’ ability to manage and enforce policies across modern infrastructure and delivery environments. Manual processes, inconsistent controls, and fragmented ownership further undermine enforcement. Policy-as-code (PaC) offers a path to codifying and automatically evaluating policies for enforcement but blindly rushing to adoption carries its own risks. This research offers a step-by-step framework to understand PaC’s potential value and your organization’s readiness for adoption.
PaC is sometimes approached as an out-of-the-box enforcement solution, without understanding the strategic, cultural, and procedural shifts required for successful adoption. IT and security leaders must treat PaC as a strategic initiative to be carefully evaluated for suitability and alignment with the security and compliance needs of the organization. Without that foundation, implementing PaC risks codifying existing problems, heightening risk, and degrading delivery performance instead of solving issues.
1. Assess before you adopt.
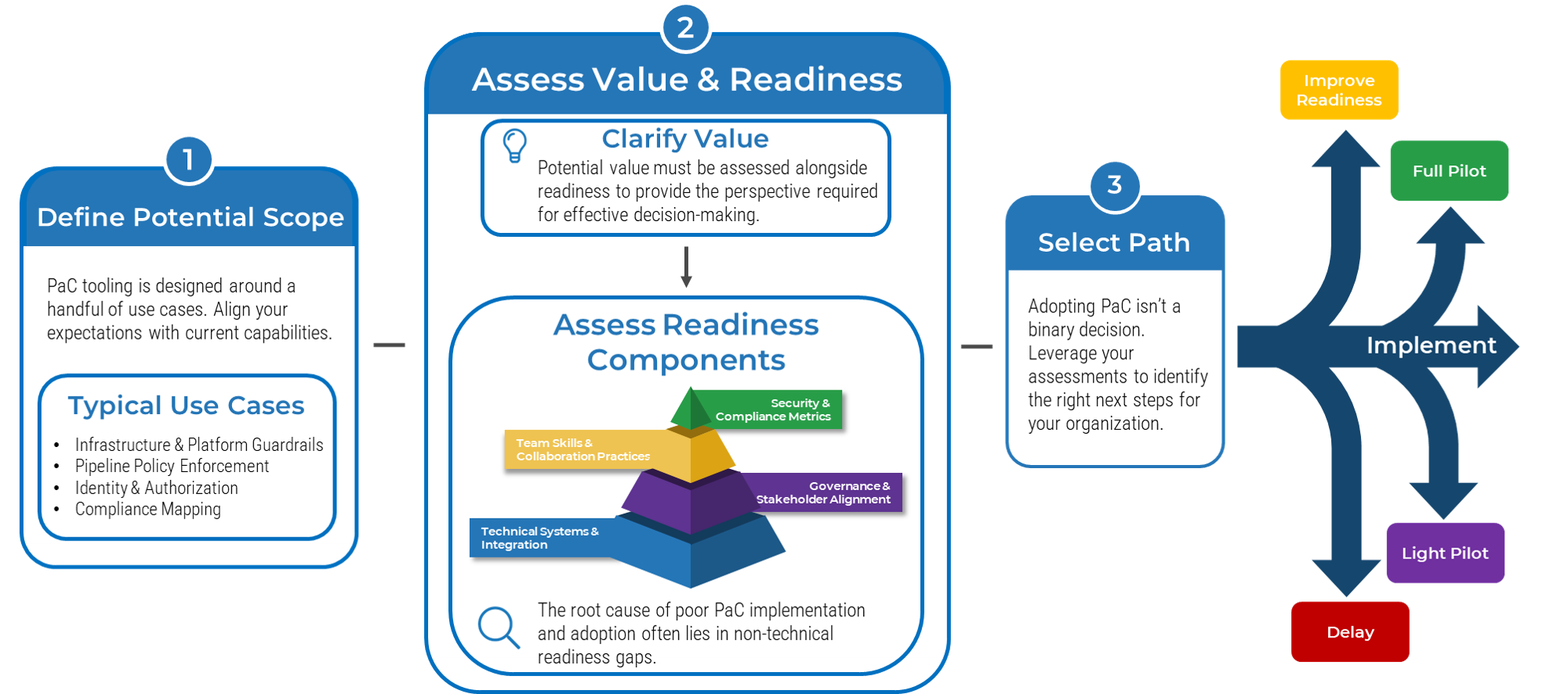
Treating PaC as plug-and-play automation creates more problems than it solves. Effective adoption starts with an assessment of PaC’s value and a multidimensional view of the organization’s readiness, spanning technical integration, governance, team skills, and metrics. Without this context, PaC risks adding overhead instead of meaningful benefits.
2. Clarify value to gain perspective.
Before investing effort into PaC, organizations must assess whether it will solve their unique challenges. IT leaders must clarify where PaC can drive value – such as compliance automation, infrastructure guardrails, or audit readiness – and whether the organization is ready to unlock that value.
3. Look beyond technical capabilities.
On its own, PaC is just a tool. Deploying it effectively will hinge on the quality of your policies, policy governance structures, and team skills. If those fundamentals are weak, PaC’s benefit to your organization will be limited.
Use this step-by-step research to determine your organization’s readiness for policy-as-code adoption
Our research offers a multistep framework supported by a value and readiness assessment tool to evaluate your organization’s PaC suitability and preparedness. Use these insights and resources to identify where automation can support policy management and enforcement and chart a path to adoption.
- Complete the value drivers and readiness surveys to understand the potential benefits of PaC for your organization and identify readiness gaps.
- Review the results of your assessments using a decision matrix to determine whether to move forward, delay, or improve readiness before adoption.
- Develop next steps to improve readiness, if needed, by reviewing current and target states and using a component-based approach to identify areas where PaC readiness can be improved across four categories.
Assess Readiness and Value for Policy-as-Code
Chart the right path toward value realization with automated policy management.
Analyst perspective
Get clarity on value and readiness before adopting or dismissing policy-as-code.
The concept of policy-as-code (PaC) – the idea that policies can be codified and automatically evaluated for enforcement – emerged about a decade ago as a response to fragmented policy enforcement and the operational strain faced by security and compliance teams. Yet, despite growing interest in PaC and success stories from large enterprises, adoption by most organizations remains relatively limited.
The fact that PaC remains underutilized is especially surprising given the mainstream adoption of automation in modern DevOps workflows and infrastructure-as-code (IaC), which provide a strong technical foundation for PaC implementation. However, this exact disconnect highlights a key barrier to PaC adoption for many organizations: not the lack of a technical foundation but the lack of stakeholder awareness – of PaC as a whole, or of the non-technical readiness required to adopt it successfully and realize its true benefits.
In the right organizational context, PaC adoption is more than a tooling rollout: it's a strategic process that brings stakeholders together, clarifies true policy intent, and establishes enforceable defaults. Conversely, treating PaC as a plug-and-play extension of IaC risks premature implementation that only codifies chaos, heightens security risk, and degrades delivery performance.
Treat PaC like the strategic initiative it is, and take the time to understand how it fits your organization, the value it offers, and whether you're ready to adopt it.

Seva Ioussoufovitch
Senior Research Analyst, Security & Privacy
Info-Tech Research Group
Executive summary
Your Challenge
Security and compliance policies are inconsistently enforced due to manual processes, undocumented or variable controls, fragmented ownership, and lack of coordination.
Traditional processes can't keep up: policy changes outpace change management, manual audits add significant overhead, and late-stage reviews bottleneck delivery.
Policy-as-code (PaC) is emerging as a core capability for automated enforcement, but your organization has not effectively adopted it.
Common Obstacles
Some stakeholders lack awareness of PaC or may be resistant to change. PaC remains a relatively niche topic, which many stakeholders approach with caution or uncertainty.
Others view PaC as a plug-and-play, policy enforcement panacea, and rush implementation while overlooking critical readiness components that are necessary for effective adoption.
PaC initiatives stall due to unclear policy governance processes, insufficient team technical skills, and inadequate integration strategies.
Info-Tech's Approach
Thoughtfully assess your unique organizational context before implementing PaC:
Confirm key value drivers and clarify how PaC will deliver meaningful value to your organization.
Evaluate readiness across multiple dimensions including technical foundations, governance models, and team skills.
Use the results of your assessments to define next steps. Develop targeted actions to improve readiness and support effective PaC adoption.
Info-Tech Insight
Treating PaC as plug-and-play automation will create more problems than it solves. Effective PaC adoption begins with an evaluation of value and a multidimensional view of readiness that considers technical integration, governance, team skills, and metrics. This context is critical to determining whether PaC will deliver meaningful benefits to your organization or just add unexpected overhead.
Your challenge
Consistent enforcement remains elusive, despite advances in tooling and automation.
- Organizations still struggle with inconsistent enforcement of security and compliance policies. This inconsistency, which spans development, staging, and production environments, is driven by manual processes, undocumented or inconsistent controls, fragmented ownership, and limited coordination. In large enterprises, frequent team transitions and M&A activities further compound these challenges.
- Policy automation lags delivery automation. Despite the growing adoption of both infrastructure-as-code and automation in modern DevOps practices, only 30% of organizations report using policy-as-code (PaC) in a significant capacity for compliance automation.
Identifying key barriers to the adoption of automation best practices demands a careful assessment of an organization's unique context beyond technical readiness to implement.
| 5% | Only 5% of CISOs consider their compliance program to be optimized. Source: The CISO Society, 2025. |
| 30% | Less than a third of organizations report using policy-as-code in a significant capacity. Source: Styra, 2023. |
Your challenge
Traditional processes are struggling to keep up.
- The pace and volume of regulatory change is rising. 85% of executives say compliance requirements have become more complex (PwC, 2025), and nearly half of compliance professionals struggle to keep up with changes (Regology, 2025).
- Gathering evidence and audit management are top challenges that add significant overhead. Vanta estimates that teams are losing four to five hours per week to manual monitoring and evidence collection that could be automated (Vanta, 2024).
- Late-stage reviews bottleneck delivery. 81% of security reviews take over a business day, which creates unacceptable deployment bottlenecks and leads organizations to skip over them altogether (CrowdStrike, 2024).
As legacy processes struggle to keep pace with today's requirements, automation shifts from an operational nice-to-have to a core capability for maintaining both control and velocity.
| 44% | 44% of compliance professionals have difficulty keeping up with regulatory changes. |
| 48% | 48% of CISOs list evidence gathering as a top challenge when implementing frameworks. |
| 54% | Just over half of major code changes get a full security review before deployment. |
Common obstacles
Effective automation requires awareness and understanding.
- Some leaders and team members lack awareness of PaC or may be resistant to change. Effective adoption requires stakeholder understanding and buy-in, but PaC remains a relatively niche topic that many stakeholders may be cautious or hesitant about.
- Others may view PaC as a plug-and-play, policy enforcement panacea. Underestimating the scope and effort of PaC initiatives leads to rushed pilots that overlook the critical readiness components that are necessary for effective and scalable adoption.
- Lack of readiness leads to a lack of progress. Even if some implementation progress is made, a lack of clear policy governance processes, team technical skills (e.g. authoring policies as code), and integration strategies can cause initiatives to stall or experience significant performance challenges.
| 88% | Most organizations report facing obstacles preventing them from using or scaling PaC. |
| 26% | Over a quarter of organizations cite lack of PaC awareness as a key adoption barrier. |
27% |
27% of developers and technical decision-makers say writing efficient policies as code is a major performance challenge. |
What is policy-as-code?
First, let's define "policy."
- In the context of policy-as-code (PaC), a policy is a codified requirement. It defines explicit rules and conditions that must be true for an action to be allowed or denied and is expressed in a machine-readable format.
- Many organizations create PaC policies mapped to external compliance frameworks. As such, vendors often offer pre-built policy packs to streamline policy creation and support alignment with these standards.
- Compared to what is typically meant by "policy" in traditional governance, risk, and compliance, policies in PaC are specific, measurable, and enforceable through automation (e.g. All EC2 instances must have a "Name" tag.)
How do we codify policies?
- Languages such as Rego, YAML, or Python are used to express policies as code; this code is stored in version-controlled repositories and is managed using standard SDLC processes such as testing or peer review.
- Decoupling of policy logic from system logic allows policies to be easily reused and consistently enforced across diverse environments.
Policy-as-Code Definition
Policy-as-code (PaC) is a method of defining policies using code and evaluating that code with a policy engine that checks inputs against declared rules and returns an explicit decision, typically in real-time (e.g. allow, deny, warn). This method is used to embed dynamic, automated enforcement directly into operational and development workflows.
Related Terms: Security/Compliance-as-Code
While the terms security-as-code and compliance-as-code are often used interchangeably with PaC, they are sub-concepts under the broader PaC umbrella. Security-as-code is specifically focused on security controls and policies, while compliance-as-code is focused on codifying regulatory and compliance requirements.
Understand policy-as-code architecture
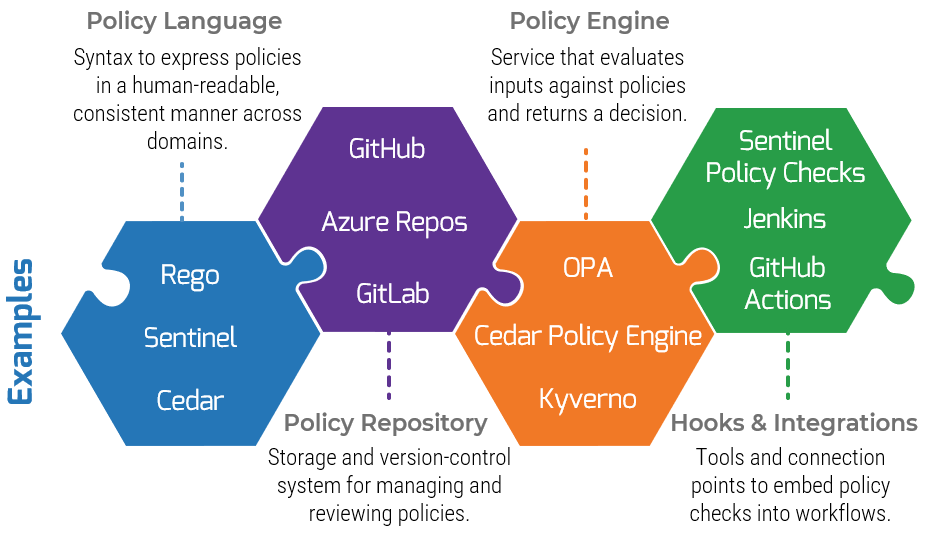
Policy frameworks or platforms, such as HashiCorp Sentinel or OPA Gatekeeper, typically offer some combination of a policy engine, a repository, and integrations together in a bundle that can be used to define, evaluate, and manage policies for a specific domain or system.
Some Common Misconceptions
"PaC can be applied to any policy."
Not all policies can (or should) be codified. Many policies are too ambiguous, context-dependent, or qualitative to express as code. Beyond codification, PaC also requires clear enforcement points where rules can be applied, and tooling is usually designed to work in several specific technical domains.
"There are vendor tools that provide a complete PaC solution."
While vendors provide platforms and frameworks to streamline PaC adoption, PaC is not plug-and-play. Organizations must still perform critical tasks such as defining enforcement points, designing and maintaining policies, managing integrations, and handling exceptions.
Assess readiness and value for policy-as-code
Info-Tech Insight
Treating PaC as plug-and-play automation will create more problems than it solves. Effective PaC adoption begins with an evaluation of value and a multidimensional view of readiness that considers technical integration, governance, team skills, and metrics. This context is critical to determining whether PaC will deliver meaningful benefits to your organization or just add unexpected overhead.
Insight summary
Assess before you adopt
Treating PaC as plug-and-play automation will create more problems than it solves. Effective PaC adoption begins with an evaluation of value and a multidimensional view of readiness that considers technical integration, governance, team skills, and metrics. This context is critical to determining whether PaC will deliver meaningful benefits to your organization or just add unexpected overhead.
Clarify value to gain perspective
Since PaC adoption demands significant effort and alignment, potential value must be assessed alongside readiness to provide the perspective required for effective decision-making.
Look beyond technical capabilities
Effective PaC adoption hinges on the quality of your policies, policy governance structures, and team skills. Don't underestimate the importance of these components when assessing readiness.
Chart an informed path forward
Adopting PaC is not a binary decision. Leverage the information provided by your assessments to determine the right next steps for your organization.
Ground your expectations
Though the definition of PaC may seem broad, current tooling and integration strategies are designed around a handful of common use cases. Align your expectations with current capabilities.
Build cross-team ownership
Sharing ownership of the definition, implementation, and evolution of PaC across security, governance, platform, and development teams is essential to improving enforcement without impeding delivery.

 Build a Cloud Security Strategy
Build a Cloud Security Strategy
 Identify the Components of Your Cloud Security Architecture
Identify the Components of Your Cloud Security Architecture
 Identify Opportunities to Mature the Security Architecture
Identify Opportunities to Mature the Security Architecture
 Secure Your Hybrid Workforce
Secure Your Hybrid Workforce
 Ensure Cloud Security in IaaS, PaaS, and SaaS Environments
Ensure Cloud Security in IaaS, PaaS, and SaaS Environments
 Improve Email Security
Improve Email Security
 Secure Your Perimeterless Network
Secure Your Perimeterless Network
 Develop a Strategic Plan for Intelligent Application Security
Develop a Strategic Plan for Intelligent Application Security
 Assess Readiness and Value for Policy-as-Code
Assess Readiness and Value for Policy-as-Code